Operations | Monitoring | ITSM | DevOps | Cloud
Go beyond basic uptime and performance monitoring with Splunk Synthetic Monitoring
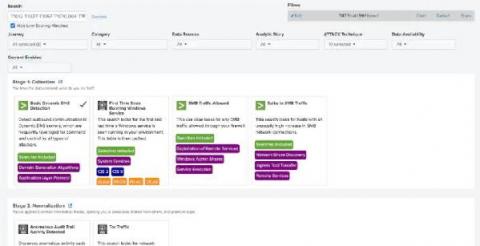
Get Started with Splunk for Security: Splunk Security Essentials
Continuing to ride the waves of Summer of Security and the launch of Splunk Security Cloud, Splunk Security Essentials is now part of the Splunk security portfolio and fully supported with an active Splunk Cloud or Splunk Enterprise license. No matter how you choose to deploy Splunk, you can apply prescriptive guidance and deploy pre-built detections from Splunk Security Essentials to Splunk Enterprise, Splunk Cloud Platform, Splunk SIEM and Splunk SOAR solutions.
Prioritize and resolve performance defects with Splunk Web Optimization
Detect any issue with Splunk APM before it turns into a customer problem
Deep Learning Toolkit 3.6 - Automated Machine Learning, Random Cut Forests, Time Series Decomposition, and Sentiment Analysis
We’re excited to share that the Deep Learning Toolkit App for Splunk (DLTK) is now available in version 3.6 for Splunk Enterprise and Splunk Cloud. The latest release includes: Let’s get started with the new operational overview dashboard which was built using Splunk’s brand new dashboard studio functionality which I highly recommend checking out. You can learn more about it in this recent tech talk which you can watch on demand.
How to Instrument a Java App Running in Amazon EKS
As we start to see big moves from monolith deployments to microservices, the adoption of Kubernetes has become top of mind for many SREs. Organizations can leverage the open-source system to automate deployments, scale, and manage containers, making Kubernetes one of the primary solutions for delivering workloads. However, maintaining the system can be difficult and, in some cases, overwhelming.
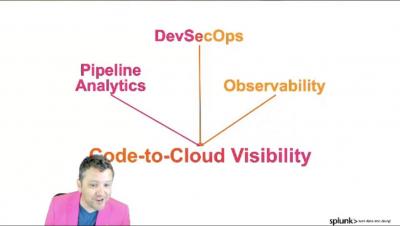
Dissecting DevOps - Code-to-Cloud Visibility: The Framework for DevOps Success
Detecting Trickbot with Splunk
The Splunk Threat Research Team has assessed several samples of Trickbot, a popular crimeware carrier that allows malicious actors to deliver multiple types of payloads.