Operations | Monitoring | ITSM | DevOps | Cloud
VMware Monitoring: Complete Guide
The dawn of virtualization and virtual machines or VMs have brought about massive changes in the industrial and commercial sector. Every organization, be it large or small, are now implementing virtual machines on different scales, and it’s saving them a lot of money and resources. But while virtualization is an incredibly powerful computing technology, it is by no means simple to handle.
IT Change Management Guide - How to Manage Changes in your IT Operations?
IT change management is one of the most important aspects of your service management and IT operations—so much that it can make or break an IT enterprise. In this blog, let’s go through what changes are, in the context of IT operations, and how to set up an IT change management function and go about managing changes in your IT ecosystem. Read on.
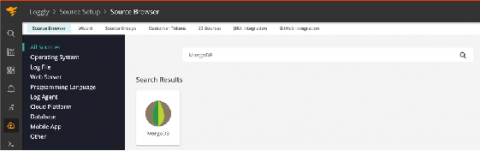
Using SolarWinds Loggly With MongoDB New Structured Logs
Just Released: 2020 Gartner Magic Quadrant for ITSM Tools Recognizes Ivanti a Leader
We’re in the early autumn season here in the northern hemisphere, with the weather getting cooler and the nights longer. That growing chill in the evenings encourages staying inside and reading by a fire for enjoyment and enlightenment.
Developing a Dedicated Log Collection & Management Plan
When it comes to your network and server processes, one of the key ways your IT team will collect data and insight is through event logging. Collecting the right event data will help inform both essential processes and services, as well as your network security measures, which is why having the proper collection plan in place is key. At Pandora FMS, we offer a host of comprehensive log collection and network monitoring solutions designed to be easily customized.
The Ultimate Guide to AWS DynamoDB
DynamoDB is a key-value and document database with single-digit millisecond response times at any scale. It’s a fully managed durable database with built-in security, backup and restore capabilities. A keyword you’ll often hear with DynamoDB is that it is a NoSQL database, which simply means it doesn’t use the traditional SQL query language used in relational databases.
How Long Should You Hang Onto Your Data?
One of the most common questions that businesses operating under GDPR, LGPD or other similar data regulations have is how long should you keep data? As answers to this question typically seem to vary widely to clear up confusion, we’ve gathered insights from business leaders & specialists across a variety of industries to try and answer this question and shed light on what are reasonable timeframes to keep hold of data, whether that may be financial, employee or other potentially sensitive data.
Support via Emoji
Emojis are finally useful for more than sentiment or sass. Cloudsmith Engineering can now be raised in emergency situations via a single emoji - SOS. And it’s been used for the first, and so far only, time. At Cloudsmith, we pride ourselves on our reactive (and in many cases proactive) support. We architected and built the platform with monitoring in mind allowing us to provide transparency of internal operations to you and us.
3 Ways to Send Emails with Ruby
For many developers, Ruby on Rails framework not only allows them to build web applications, websites, and efficient database solutions, but it can help them optimize mailing operations. You can easily use Ruby on Rails mailer, an automatic tool to build transactional messages of any kind, and make proper authentication. In this article, we review three main ways to work with email sending in RoR, which include some Ruby gems, the Net::SMTP class, and the facilities of the Socket system.