Operations | Monitoring | ITSM | DevOps | Cloud
Latest Posts
The First 48 Hours of Ransomware Incident Response
The Cybersecurity Threat Landscape in 2024
Meeting the SEC's New Cybersecurity Rules: How Flowmon Empowers Companies to Comply
Application-down Troubleshooting Through the Eyes of a Network Engineer
Imagine yourself wearing the hat of a network engineer, where no two days at work are alike. In this dynamic environment, you're often the first point of contact when something remotely IT-related goes wrong, with users frequently pointing fingers at the network. Yet, your expertise lies in knowing the intricacies of network traffic, a vital skill for addressing operational and performance challenges.
What is Zero Trust and How IT Infrastructure Monitoring (ITIM) Makes it Happen
When the concept of Zero Trust emerged in 2010, it marked a sea change in how IT and network security are handled. The term, invented by Forrester Research analyst John Kindervag, is loosely based on the “never trust, always verify” motto. So why is this a sea change? Before 2010, IT focused on perimeter defenses and the concept of DMZs — areas of the network they deemed safe based on the protection they implemented.
Meeting the SEC's New Cybersecurity Rules: How Flowmon Empowers Public Companies To Comply
The much-anticipated cybersecurity rules by the U.S. Securities and Exchange Commission (SEC) for public companies have arrived, signaling a significant step forward from the proposed rules released in March 2022. These final rules, effective July 26, 2023, introduce new obligations that public companies must adhere to, promising a more secure and transparent corporate landscape. However, these regulations bring significant compliance challenges and litigation risks.
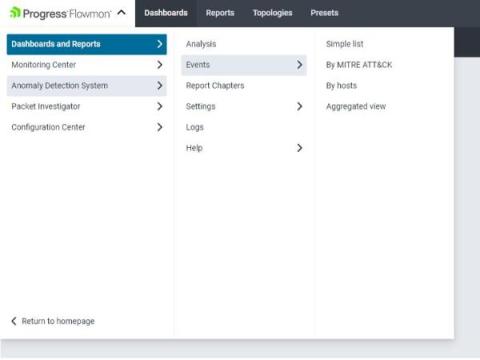
What is new in Flowmon 12.3 & ADS 12.2
At Progress Flowmon, we continue to develop and improve the Flowmon product family. The latest update takes the core Flowmon product to release 12.3 and updates our industry-leading Anomaly Detection System (ADS) to version 12.2. In this blog, we highlight several of the improvements.
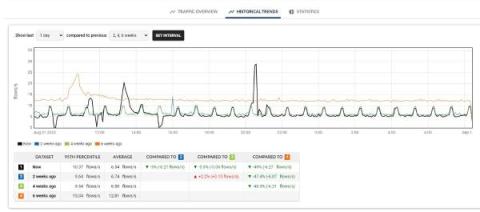
Introducing Historical trends to enable proactive problem detection and informed decision making
Historical Trends is a new functionality introduced with Flowmon 12.3 that will enable you to easily compare your current network traffic with historical values and gain new valuable insights.
Augmenting behavior-based network detection with signature-based methods
Network detection tools utilize one of two prominent approaches for threat detection: AI-driven behavior-based methods capable of identifying early indicators of compromise, and signature-based ones, which flag known attacks and common CVEs. While these systems operate on distinct principles, their combination forms more robust defense mechanism, helps to consolidate tools, provides richer threat context and improves compliance.