How to enable signature-based detection in Flowmon Probe and Flowmon ADS
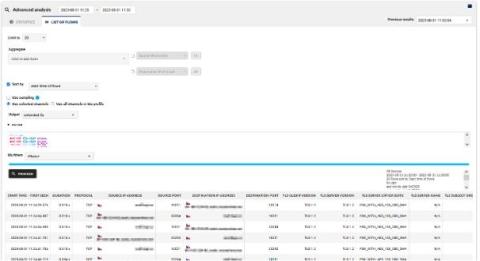
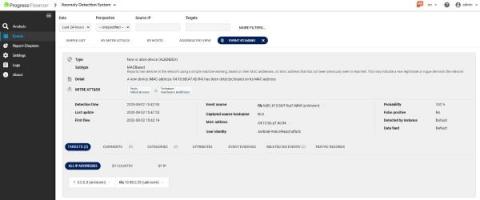
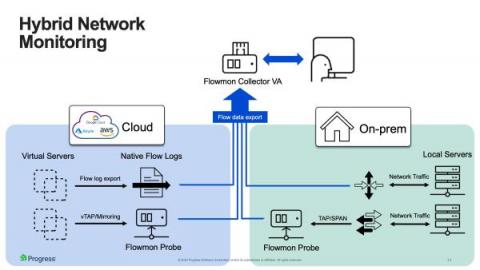
In this article, we explained the benefits of combining signature-based detection by Suricata IDS with behavior-based detection by Flowmon ADS. Now, let’s talk about how to enable this feature using Flowmon Probe and Flowmon ADS.