Operations | Monitoring | ITSM | DevOps | Cloud
Latest News
Storing Secrets with Telegraf
Telegraf is an open source plugin-driven agent for collecting, processing, aggregating, and writing time series data. Telegraf relies on user-provided configuration files to define the various plugins and flow of this data. These configurations may require secrets or other sensitive data. The new secret store plugin type allows a user to store secrets and reference those secrets in their Telegraf configuration file.
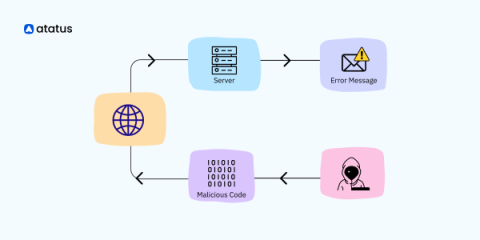
Data Tampering: A Comprehensive Guide
In an increasingly interconnected and data-driven world, where information shapes decisions and fuels innovation, the integrity of data has become paramount. However, lurking beneath the surface is a silent threat that can undermine trust, compromise systems, and wreak havoc on organizations: data tampering. In this post, we delve into the realm of data tampering, exploring the vulnerabilities, the reasons behind data tampering practices, and countermeasures against them.
Digital Leap: Understanding the Transformative Impact of Software on Healthcare
The ABC of Risk Management Automation
It's Official, Scout is SOC 2 Certified
Valued customers, friends, and Scout APM users: Our goal has always been to provide you with the peace of mind of knowing your systems are healthy and serving your customers as expected. While security has always been paramount to us, we’ve recently made it official. We are thrilled to share with you a recent significant achievement for our team and those who trust us with their data. After many months of hard work, we have obtained our SOC 2 certification!
What is Zero Trust Security and Why Should You Care?
Automation has become a game changer for businesses seeking efficiency and scalability in a rather unclear and volatile macroeconomic landscape. Streamlining processes, improving productivity, and reducing incidence for human error are just a few benefits that automation brings. However, as organizations embrace automation, it’s crucial to ensure modern security measures are in place to protect these new and evolving assets.
What Do Our Users Love About Cove Data Protection?
At N-able’s recent Empower partner event in Prague, we took the opportunity to ask some Cove Data Protection users what they actually think about the product. Naturally, we were pleased to hear so many positive comments, but we also found that their reasons for choosing Cove varied, as did the capabilities they value most. Here’s a little sample.
10 Most Common PHP Security Threats and the Best Ways to Fix Them
PHP is a powerful language used by at least 80% of all the applications you use today as their backend scripting language. This can be attributed to its relatively simpler syntax, which is on the same line as other C-style languages. It supports different operating systems (Windows, Linux, macOS), web servers, databases and integrates seamlessly with popular databases like MySQL, PostgreSQL, and Oracle, making it a suitable choice for database-driven applications.
A guide to dynamic application security testing (DAST)
Dynamic application security testing (DAST) is a critical security measure for modern software delivery pipelines. It involves evaluating the security of web applications by actively testing them in real-time, simulating real-world attacks to identify vulnerabilities. As the cybersecurity threat landscape has evolved, DAST has emerged as a key tool for enforcing application security in continuous integration and continuous delivery (CI/CD) pipelines.