Operations | Monitoring | ITSM | DevOps | Cloud
Latest News
7 Ways to Prevent Network Security Breaches in the Workplace
Network security breaches are every business’s nightmare. A security breach could be anything from password attacks with further unauthorized system access to data leakage. Whether it is a small start-up or a large enterprise with millions of dollars in turnover, a single network security breach can be detrimental to the reputation of any company, not to mention the financial losses incurred. According to the 2021 Thales Data Threat Report, 45% of US companies suffered a data breach in 2020.
Why is EDR Important? A Business Case for MSPs
The security industry may not have been making a lot of noise about Endpoint Detection and Response (EDR) for long, but it’s not actually a new technology. Despite having been around now for roughly 10 years, it’s only recently that EDR has really come to the fore. This has been driven by the fact that traditional antivirus struggles to cope with the increasing sophistication of modern malware, and is certainly unfit to handle new types of cyber threats.
Top 5 Managed Detection and Response Services and How to Choose
Managed Detection and Response (MDR) is an approach to cybersecurity that combines advanced technologies, skilled analysts, and a proactive response process to detect, investigate, and remediate cyber threats. MDR is typically delivered as a service by a third-party provider and includes a range of security capabilities, such as threat intelligence, behavior analysis, anomaly detection, and incident response.
Best CMMS Software Features and Its Benefits | Infraon
Datadog Integration Update: Vulnerability Scanning and Audit Logs
The team at Cloudsmith is always looking for ways our customers and community can leverage adjacent technologies within the DevOps and application development ecosystem to secure the software supply chain. Cloudsmith developed the first integration with Datadog, the Cloud Monitoring as a Service solution, a few years ago! That integration was the first step in helping the community leverage both solutions simultaneously, strength for strength.
PagerDuty Announces New Automation Enhancements That Simplify Operations Across Distributed and Zero Trust Environments
Be sure to register for the launch webinar on Thursday, March 30th to learn more about the latest release from the PagerDuty Operations Cloud. Rundeck by PagerDuty has long helped organizations bridge operational silos and automate away IT tasks so teams can focus more time on building and less time putting out fires. And while this mission still rings true today, our vision is to extend this reality and revolutionize all operations while continuing to build trust.
How to properly check if files are readable
Opening and reading files may cause your program to block indefinitely, which is a major problem for configuration management tools like CFEngine. What if we make a program that can check if these file operations would block indefinitely, before using them? Unfortunately our good friend Alan Turing proved that such programs are not theoretically possible.
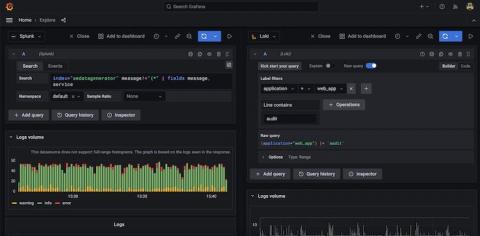
Reduce compliance TCO by using Grafana Loki for non-SIEM logs
Compliance is a term commonly associated with heavily regulated industries such as finance, healthcare, and telecommunication. But in reality, it touches nearly every business today as governments and other regulatory agencies seek to enact tighter controls over the use of our collective digital footprint. As a result, more and more companies need to retain a record of every single digital transaction under their control.
Best Practices for SOC Tooling Acquisition
Your Security Operations Center (SOC) faces complex challenges for keeping corporate data safe and in the right hands everyday. The right tooling is critical for success. Deciding when—and how—to make investments in SOC tooling is complex and challenging across organizations. There’s a ton of vendor spin out there and it’s important to understand what’s real and what isn’t.