Operations | Monitoring | ITSM | DevOps | Cloud
Latest News
New in Grafana roles: Manage user permissions better with 'No basic role'
Since we introduced role-based access control (RBAC) in Grafana 9.0, users — and later, service accounts — have been required to have an assigned role that includes a basic set of permissions. This sometimes led organizations to create users and service accounts that had more permissions than necessary. As a result, Grafana administrators had to make additional adjustments to users’ permissions on a case-by-case basis.
Navigating Security Challenges in Kubernetes Orchestration Platforms
As Kubernetes solidifies its position as the standard for container orchestration, it’s imperative to examine the associated security challenges. Kubernetes brings powerful capabilities to the enterprise and introduces new attack vectors and potential vulnerabilities. Here at Kublr, we sat down with our best experts to discuss how our team solves security challenges and how Kublr helps clients mitigate them.
Turkeys, Tech, and Table Settings: A Humorous Guide to IT Security at Thanksgiving Dinner
Let’s set the table a bit. As you know, in the U.S., Thanksgiving is coming up. And recently I had a conversation with my 83-year-old mother about Thanksgiving. Of course, we came across the inevitable parallels between Thanksgiving dinner and network security! That’s what you would be thinking when talking about Thanksgiving dinner with someone right? Before we dive into the feast, let me set the table.
Digital Transformation Is Changing the Mortgage Industry - Here's How
ISO 27001 Compliance: Everything You Need to Know
Let’s talk about what ISO 27001 compliance means for the tech team. If you’re a CTO, DevOps team lead, or cyber security specialist, you’ll have a lot of plates spinning at any given point in time. You need to ensure and maintain security protocols and compliance without hindering the development team’s ability to test and deploy new code (often at scale). It’s a constant battle to align development speed with governance tasks like audit, compliance, and security.
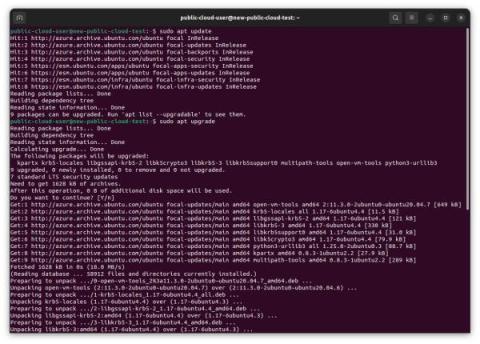
Ubuntu Explained: How to ensure security and stability in cloud instances-part 2
Demystifying FEDRAMP and NIST for Continuous Compliance
Today, federal agencies rely extensively on Cloud-based SaaS applications for everything from payment processing and document management, to data security and employee workflow automation. These tools help departments to function very efficiently, but because they are being used for essential government functions, it’s vital that they are safe and secure. For example, personnel at The Pentagon or The Department of Homeland Security can’t just choose any software vendor in the marketplace.
Network Overhead, Latency with Secure Access Service Edge (SASE)
Digital Experience Monitoring (DEM) has become an area of focus for Secure Access Service Edge (SASE) vendors. As businesses adopt SASE or security-as-a-service technology for compliance and security, they must consider the overall employee digital experience. SASE architectures add network overhead and impact performance, response times, and latency. In this article, we will delve into.