Operations | Monitoring | ITSM | DevOps | Cloud
Latest News
Why an OS Monitoring tool is not sufficient for Monitoring VMware and Other Virtualization Technologies
You have management software that you’ve used for your Linux or Windows servers. Can’t you just deploy a Linux agent and monitor a VMware vSphere/ESX server, or a Windows agent to monitor a Microsoft Hyper-V server? This is a very common question that comes up in any discussion on VMware monitoring and virtualization management. After all, when a VMware ESX server boots, the administrator gets to a Linux login prompt and can login to a Linux operating system.
What is SIEM?
SIEM (Security Information and Event Management) is a kind of software whose purpose is to provide organizations and corporations with useful information. “About what?” you may wonder. Well, about potential security threats related to your business networks. SIEM does this through data collation and by prioritizing all kinds of dangers or threats. In general, we already answered the question “what is SIEM?”, but how does it do it?
The Path of an Outlaw, a Shellbot Campaign
Serverless Logging Performance, Part 2
When thinking about serverless applications, one thing that comes to mind immediately is efficiency. Running code that gets the job done as swiftly and efficiently as possible means you spend less money, which means good coding practices suddenly directly impact your bottom line. How does logging play into this, though? Every logging action your application takes is within the scope of that same performance evaluation.
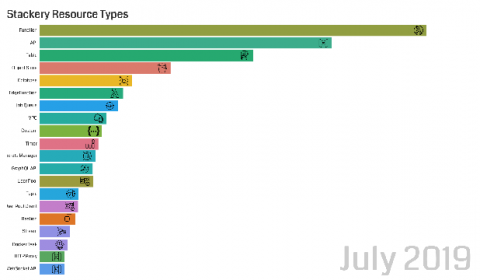
A Timeline of Resource Use
I’m a bit of a data nerd. And like many fortunate people, I’m still working from and generally staying home and have a lot spare time on my hands. So what does that combination result in? Graphs!
Splunk Insights EOL: Infrastructure and AWS Cloud Monitoring
Two years ago we introduced Splunk Insights for AWS Cloud Monitoring and Splunk Insights for Infrastructure on the AWS Marketplace as a Pay-As-You-Go Amazon Machine Image, where you could initiate an instance and pay hourly to use these products after a 15-day trial. Assessing our portfolio, we are discontinuing these offerings to focus on differentiating capabilities, namely the ability to search and apply machine learning to your data in addition to visualizing insights.
Detecting Malware and Watering Hole Attacks with Splunk UBA
You may be surprised to learn that a particular malware is responsible for data theft in over 20% of financial institutions and other verticals in 2019. Watering hole attacks involve a web server that hosts files or applications where the website or files on the site become weaponized with malware. While recent news cycles have shined a spotlight on ransomware and crimeware, malware is not a new concept.
Three reports to ensure your project plans are failproof
Efficient project planning is an important skill for project managers. It helps you get things done on time, make iterations, and develop contingency plans for emergencies.
Take website, API & server availability monitoring to the next level
People throw the terms “availability” and “uptime” around a lot, but depending on what you’re monitoring, the definition of these terms may change. In this article we use the narrow definition, accessible, to explore the various options Uptrends has for checking availability on websites, APIs, and servers.