Operations | Monitoring | ITSM | DevOps | Cloud
Compliance
CIS benchmark compliance: Introducing the Ubuntu Security Guide
The CIS benchmark has hundreds of configuration recommendations, so hardening and auditing a Linux system manually can be very tedious. Every administrator of systems that need to comply with that benchmark would wish that this process is easily usable and automatable. Why is that? Manual configuration of such a large number of rules leads to mistakes – mistakes that cause not only functional problems, but may also cause security breaches.
Ubuntu introduces the Ubuntu Security Guide to ease DISA-STIG compliance
January 17th: London, UK – Canonical, the company behind Ubuntu, the world’s most popular operating system across private and public clouds, now offers the Ubuntu Security Guide tooling for compliance with the DISA Security Technical Implementation Guide (STIG) in Ubuntu 20.04 LTS. The new automated tooling builds on Canonical’s track record of designing Ubuntu for high security and regulated workloads, powering U.S. government agencies, prime contractors, and service providers.
How to achieve CIS Compliance with Puppet
Security compliance is the new black. Everyone is talking about it. Everyone is writing about it. Hopefully everyone is doing something about it, but it's a big lift for organizations. Compliance can mean adhering to departmental and company standards; it can mean well-defined regulatory standards like HIPAA, GDPR, and others. Compliance can mean adopting a standardized set of recommended protocols for cyber security. If compliance isn't on your radar right now, it should be.
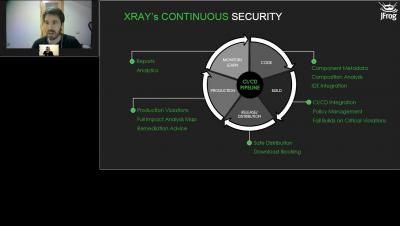
Kroger Uses JFrog Xray for Software Security and License Compliance
Blancco's Data Erasure Solutions Empower DoD Contractor Compliance with CMMC 2.0 Media Protection Requirement
IT Ops' role in strengthening security and achieving compliance
It wouldn’t be Cybersecurity Awareness month without some spooky-themed blogs with language focused on Fear, Uncertainty, and Doubt (FUD). Luckily, it’s the end of November now, and this isn’t that kind of blog, but what was true in October is still true today. I won’t tell you that you need to be afraid of bad actors infiltrating your security defenses and wreaking havoc in your infrastructure. Why? Because you are likely stressed enough already. Don’t you think?
How Automation Takes the Time and Guesswork Out of Security Compliance
Episode 1: DevSecOps Coffee Break Series Add OSS Security & Compliance to Artifactory
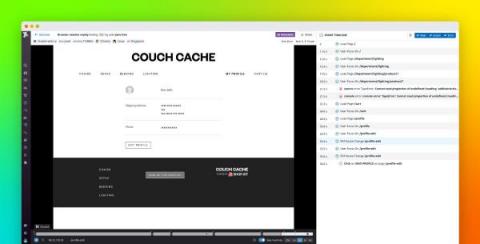
Obfuscate user data with Session Replay default privacy settings
Session Replay enables you to replay in a video-like format how users interact with your website to help you understand behavioral patterns and save time troubleshooting. Visibility into user sessions, however, can risk exposing sensitive data and raise privacy concerns. For example, a user session may include typing in a credit card or social security number into an input field.