Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on Cloud monitoring, security and related technologies.
How To Handle Untaggable And Untagged Cloud Spend
Self-hosted versus cloud-based mobile app testing
Testing is a vital part of the mobile app development process. Your team can use testing to evaluate the quality, security, and reliability of mobile apps before releasing them to your users. Users who expect their applications to be highly performant and intuitive. There are two ways DevOps teams can perform testing for mobile apps: on-premise (also called self-hosted) or in the cloud. But which of these is the best option for your team?
State of Cloud Cost Report 2022
Cloud migration efforts continue to grow today as organizations move into a post-pandemic work environment. According to McKinsey & Company, by 2024, most enterprises aspire to have $8 out of every $10 for IT hosting go toward the cloud. In a survey by Morgan Stanley, CIOs say cloud computing will see the highest rate of IT spending growth in 2022.
AWS Monitoring Tool
Automate AWS Lambda function deployments to AWS CDK
When you build a cloud-based application, you can choose to deploy the resources using the GUI (Graphical User Interface) or CLI (Command Line Interface) provided by the cloud provider. This approach can work well with just a handful of resources, but as the complexity of your application increases, it can become difficult to manage the infrastructure manually.
Amazon Photos Alternative? The Good, the Bad, and More Private Options
Seven Tools to Help You Become a Better Serverless Developer
Serverless technologies let us do more with less effort, time and energy. They let us focus on creating user value and let the cloud handle undifferentiated heavy-lifting like scaling and securing the underlying infrastructure that runs our code. Serverless technologies have allowed me to accomplish tasks as a solo engineer that used to take a whole team of engineers to accomplish, and I’m able to complete these tasks in a fraction of the time and cost to my customers.
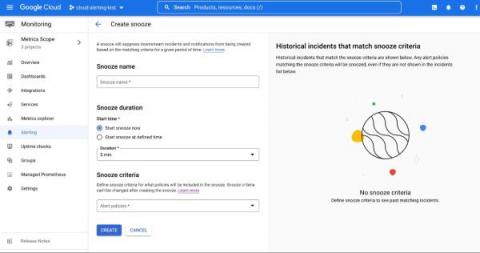
Snooze your alert policies in Cloud Monitoring
Does your development team want to snooze alerts during non-business hours? Or proactively prevent the creation of expected alerts for an upcoming expected maintenance window? Cloud Alerting in Google's Cloud operations suite now supports the ability to snooze alert policies for a given period of time. You can create a Snooze by providing specific alert policies and a time period. During this window, if the alert policy is violated, no incidents or notifications are created.