Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on DevOps, CI/CD, Automation and related technologies.
How Puppet Enterprise Does Desired State Automation at Scale
When and Why To Adopt Feature Flags
What if there was a way to deploy a new feature into production — and not actually turn it on until you’re ready? There is! These tools are called feature flags (or feature toggles or flippers, depending on whom you ask). Feature flags are a powerful way to fine-tune your control over which features are enabled within a software deployment. Of course, feature flags aren’t the right solution in all cases.
How to Build Multi-Arch Docker Images
With ARM based dev machines and servers becoming more common, it is become increasingly important to build Docker images that support multiple architectures. This guide will show you how to build these Docker images on any machine of your choosing.
How Does Docker Network Host Work?
Docker is a platform as a service product. With Docker, you can easily deploy applications into Docker containers. Containers are software "packages" that bundle together an application's source code with its libraries, configurations, and dependencies. This helps software run more consistently on different machines. To use Docker containers, you need to understand how Docker networking works. Below, we'll answer the question: "what is Docker network host?". We'll also take a look to see how it works.
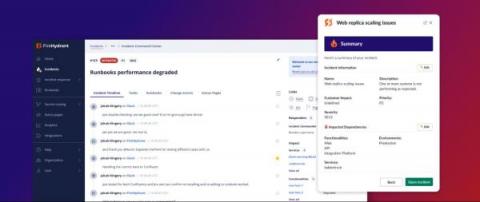
Our fully-redesigned incident response experience delivers a more intuitive workflow
Today we’re releasing fully redesigned Slack and Command Center experiences for FireHydrant so anyone on your team can intuitively navigate the incident response process — in the app or on the web. There are many things you can do ahead of an incident to help things run smoothly: design and document your process, automate predictable steps, train the team, and run drills.
Default Pull Request Tasks
Voice Network Fraud: How to Fight Back with Automated Threat Prevention
Tutorial: Setting Up AWS Observability Solution V2.4.0 Using CloudFormation Template
Testing basics | Functional vs non-functional
To learn more about functional vs non-functional testing, visit: https://circleci.com/blog/functional-vs-non-functional-testing/