Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on DevOps, CI/CD, Automation and related technologies.
Qovery is now part of the CNCF
Qovery is excited to announce that we are now a silver member of the Cloud Native Computing Foundation (CNCF) and Linux Foundation (LF). As a CNCF silver member, we are looking forward to contributing to CNCF projects and playing an active role in developing the cloud-native ecosystem. Qovery also recently makes is deployment engine open-source, an abstraction layer library that turns easy apps deployment on AWS, GCP, Azure, and other Cloud providers.
Implementing GitOps on Kubernetes Using K3s, Rancher, Vault and ArgoCD
As Kubernetes continues to establish itself as the industry standard for container orchestration, finding effective ways to use a declarative model for your applications and tools is critical to success. In this blog, we’ll set up a K3s Kubernetes cluster in AWS, then implement secure GitOps using ArgoCD and Vault. Check out the source for the infrastructure and the Kubernetes umbrella application here.
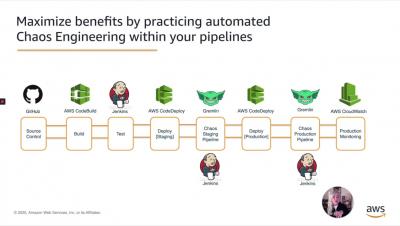
Chaos Engineering: How to create an automated Chaos Gauntlet with Gremlin and Jenkins on AWS
Tutorial: Using Helm Hooks in Your Codefresh Pipeline
When getting started with Kubernetes and Helm, the process across the release life cycle can feel like a black-box; having to follow debugging processes to understand what is going on behind the scenes. Helm hooks can help with that. This post provides an overview of: If you are new to Helm, we suggest to check-out our previous tutorial first and then come back to learn more about Helm hooks. Hooks perform a single action at a specified point during the release life cycle.
Active Directory Monitoring Essential Guide
An effective active directory monitoring system is essential to a secure directory design. There is a wide variety of security issues and loopholes that can be identified early if the users on the network are following the active directory monitoring guidelines. The lack of such monitoring can lead to a multitude of security threats which can result in financial and reputational damage along with data loss.