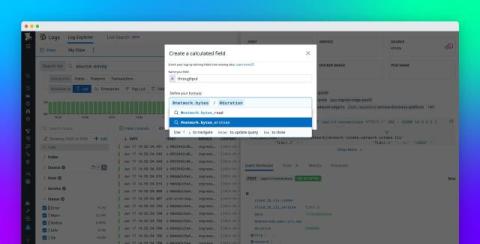
Transform and enrich your logs at query time with Calculated Fields
As the number of distinct sources generating logs across systems and applications grows, teams face the challenge of normalizing log data at scale. This challenge can manifest when you’re simply looking to leverage logs “off-the-shelf” for investigations, dashboards, or reports–especially when you don’t control the content and structure of certain logs (like those collected from third-party applications and platforms).