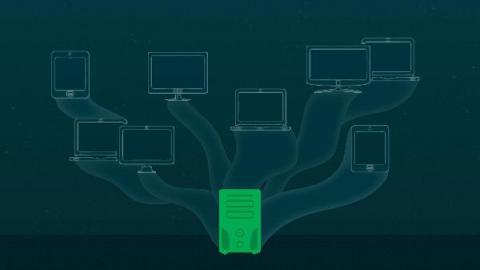
Nameserver: What is It? How Does It Work? Why It is Important to Your Website?
You may have come across the word "nameserver" if you maintain your own website. You may, however, have no true idea of what one is or how it works. Knowing a little about the “nameserver” concept can help you manage your website. Simply said, nameservers help browsers in establishing links between URLs and websites. They're essential since we'd have to memorize IP addresses to visit websites if we didn't have them.