Operations | Monitoring | ITSM | DevOps | Cloud
Introducing HA MicroK8s, the ultra-reliable, minimal Kubernetes
15th October 2020: Canonical today announced autonomous high availability (HA) clustering in MicroK8s, the lightweight Kubernetes. Already popular for IoT and developer workstations, MicroK8s now gains resilience for production workloads in cloud and server deployments. High availability is enabled automatically once three or more nodes are clustered, and the data store migrates automatically between nodes to maintain quorum in the event of a failure.
Microsoft's 3 major incidents in 10 days, where did they go wrong?
Just in case you haven’t heard, last week Microsoft experienced a huge outage that prevented users from accessing its Office 365 cloud-based subscription service which serves 200 million active monthly users. This latest outage was the third in ten days, causing the company to receive a deluge of customer complaints about a 'something went wrong' message that popped up when they tried to access their accounts.
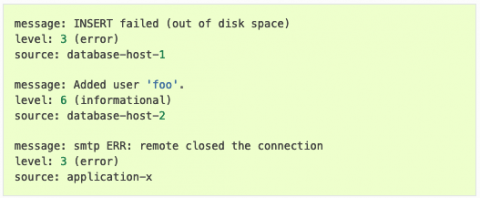
Event Log Management for Security and Compliance
Security log management is the process of collecting, storing, and correlating the network data that details all activity in your systems and networks. Every action in an organization’s network generates event data, including records produced by operating systems, applications, devices, and users. The Center for Internet Security (CIS) identifies log management as a basic control for detecting malicious actors and software hiding in networks and on machines.
Dangers of Console-Driven Development
AWS offers the ability to login to a web UI dashboard. In this dashboard, you can add, edit, and deploy various cloud resources. When I was first getting started with AWS, this is where I began for two reasons: My very first full-time job as a Software Engineer was on a small enough team that all of our infrastructure was setup using the AWS console in a single AWS account.
The impact of the page load speed on SEO
Have you ever visited a website and be extremely frustrated by the amount of time it takes to load the landing page, let alone the other pages on the site like the "About us" and "Contact" page? Well, if your answer to this question is yes, then know now that you are not alone in experiencing slow loading sites.
ServiceNow adds Health and Safety Testing app to Safe Workplace suite
At the start of the COVID pandemic, the business world shifted to remote work almost overnight, triggering a new wave of digital transformation. According to a recent study by ServiceNow in partnership with Wakefield, this was a welcome change – 87% of employees believe their company created new and better ways of working.
Integrating TA-Nix with Splunk App for Infrastructure
Previous articles in our series have introduced the Splunk App for Infrastructure (SAI) and provided getting-started guidance for Linux and Windows using native metric-collection tools such as collectd and perfmon. But did you know you can also use your existing Splunk Universal Forwarders (UF’s), together with the Splunk Add-on for Unix and Linux (TA-Nix) to send both the metrics and logs without the need of additional agents?
Why AWS Lambda Throttles Functions (and how to fix it!)
Have you noticed recently that your AWS Lambda invocation requests are getting throttled? If so, your Lambda functions are probably not running as designed. Let’s examine the possible causes and solutions to poor Lambda performance.
Jaeger Essentials: Distributed Tracing from Dapper to Jaeger
If you are dealing with microservices, serverless architecture, on any other type of distributed architecture, you have probably heard the term “Distributed Tracing.” You may have been wondering what it’s all about, and where should you start, in this post, I’ll tell you about the journey we passed at Duda, from the day we heard about distributed tracing and started to explore whether it will be useful to use it in our company, to the exploration on what is distributed tracing a