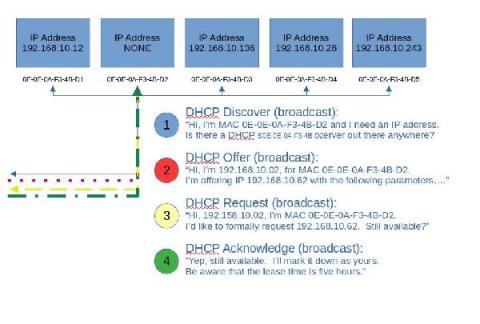
Basic DHCP concepts
Let’s step back and take a very basic look at DHCP. In fact, let’s look at the analogy of assigning a street address to your house. Usually, this is done by the local 911 dispatch office, or some other central authority. They typically use either a survey map or a latitude, longitude pair to locate you, before they assign your house numbers from a pool of available addresses, compatible with other addresses in the area.