Operations | Monitoring | ITSM | DevOps | Cloud
Good IT Support? Or Just a Pain In The Bits?
Good IT Support is harder to pin down than you’d think but deciding which technology is better than the next is pretty straightforward for most of us. Who wouldn’t pick the latest iPhone or Android device over a flip-phone? Actually, most senior citizens—but to their credit flip-phones never really die, they just regenerate into larger flip-phones. Bad example. Point is we can rate, compare, trial, and study just about every digital technology on the market.
October 2019 Update: Improved usability and new emergency alarm triggering in the app
The October update of the mobile app includes the improvements described below and the user experience includes a new feature. The user interface of the app has been improved so that you can now decide for yourself if you want to see all Signls on the dashboard differentiated by categories. Using the “More” button on the dashboard’s Signl widget, you can now open a context menu and show or hide the display of the categories.
How to Keep Malware Out of Your Printers
The landscape of cybersecurity is always changing, and new threats are constantly emerging. One of the newest – and the most interesting, if you are into that kind of thing – is the rise of printer malware. This type of malware started to be reported in November 2017, when Barracuda Labs saw an attack where cybercriminals spoofed a printer to send a malicious attachment that appeared to be a legitimate file sent by a network printer.
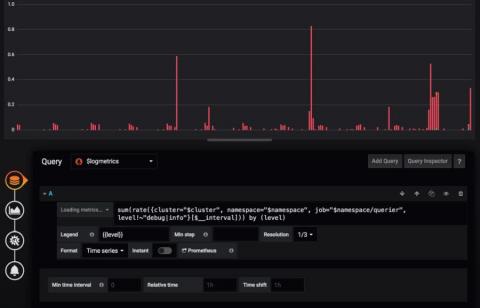
Visualizing Sensu Go data in Grafana
Monitoring systems is critical to any IT operation. For many companies, these systems are a critical business component that can have serious business impact (including expensive downtime) if these systems fail. For this reason, it is essential that you have a good monitoring system in place that you can rely on, one that notifies you early if unforeseen problems occur.
15 hours writing CloudFormation reduced to 15 minutes with Stackery
ServerlessConf NY this past October was an important milestone for those of us tracking how software is built on cloud services. . We’ve seen the serverless talks evolve from “what is serverless” to “I built a weird thing” to “We built a new business” to “We refactored a legacy app and kickstarted our feature velocity.” We’ll come back to those last two soon, , but I want to highlight some points from one in particular by Tim Wagner.
What is MTTD? Mean Time to Detect Explained In Detail
This post will answer a simple question, “What is MTTD?” The answer—or at least the start of it—was already spoiled by the post title. Sure enough, MTTD stands for “Mean time to detect.” It refers to an important KPI (key performance indicator) in DevOps. Is the question answered? Can we call it a day with that definition? Of course not.
Announcing CloudSploit for Azure
Today, CloudSploit is excited to share that our cloud security auditing solution is now publicly available for Microsoft Azure IaaS accounts. This release includes all the hallmarks of CloudSploit’s existing service for Amazon Web Services: an open source core scanning engine, PCI and HIPAA compliance program mappings, detailed security reports including recommended remediation information, links to official Azure documentation, and full support for all 42 Azure regions.
What's New in Loki v0.4.0
More frequent releases! We continue to march Loki towards the first GA release, and to help that process we are going to target bi-weekly to weekly releases, depending on changes. - Ed Welch 08/12/2019 My mistake, there was clearly a typo in my previous post, and when I said bi-weekly I clearly meant bi-monthly. ;) The good news, however, is that the project has been very busy and there are some very exciting new features in Loki v0.4.0!
JVM Tuning: How to Prepare Your Environment for Performance Tuning
When it comes to Java applications, to make sure they run at peak performance, it’s critical to close the resource gap between the code and the virtual machine it’s running on – if there is one. The way to do that is by peaking into and fine-tuning the Java Virtual Machine (JVM). However, that’s easier said than done. Many factors can influence JVM performance, and during tuning, you must consider all of them. Though, there are ways around that to make it not be such a pain.