Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on Log Management, Log Analytics and related technologies.
Securing Kubernetes with Open Source Falco and Logz.io Cloud SIEM
In a previous blog post I discussed the complexity of securing Kubernetes environments, and some best practices. Unfortunately, even if we follow best practices in setting up and configuring our system, we can never eliminate all the vulnerabilities.
Elastic's Guide to Keeping Services up and Running with Real-time Visibility
Getting started with Grafana Loki - under 4 minutes
Fastly Logs Insights
This tutorial will show you how can Coralogix provide analytics and insights for the Fastly logs you ship to Coralogix, both performance, and security.
Working with Solr Plugins System
Apache Solr was always ready to be extended. What was only needed is a binary with the code and the modification of the Solr configuration file, the solrconfig.xml and we were ready. It was even simpler with the Solr APIs that allowed us to create various configuration elements – for example, request handlers. What’s more, the default Solr distribution came with a few plugins already – for example, the Data Import Handler or Learning to Rank.
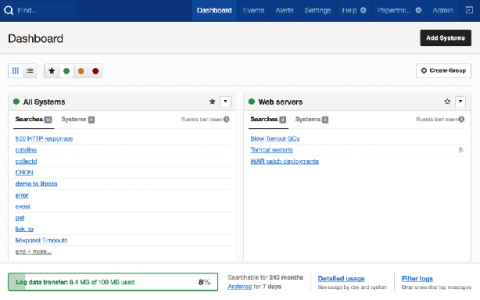
Log management: The key to centralized log aggregation and easy troubleshooting
A large number of security breaches are impacting industry verticals, including banking, financial services and insurance (BFSI), telecom, and hospitality, so there's a growing need for organizations to fortify their infrastructure against these threats. For example, by the time T-Mobile identified the intrusion and unauthorized access to its sensitive data in 2019, both its customer and employee details were already stolen by hackers.
5 Benefits of Cloud-Based Log Aggregation Tools
Limitless analytics for all your data, at a price that fits your budget
Making Machine Learning Accessible to More Users
As we connect with customers we increasingly hear the need for teams to be more predictive with their data. A big challenge is uncertainty around how to get started, especially when much of their data is unstructured. At Splunk, our goal is to make data — and machine learning — accessible for a broad range of users. The good news is, with machine learning doing even more work on your behalf, you don’t need to be a data scientist to use these advanced capabilities.