Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on IT Networks and related technologies.
April/2022 - CVE-2022-22965: Spring4Shell Remote Code Execution Mitigation
Recently, a Remote Code Execution vulnerability was discovered in the Java Spring Core library. This vulnerability allows attackers to execute arbitrary code on affected systems. You can find more information on that vulnerability in the announcement on the Spring Blog. While HAProxy Enterprise, HAProxy ALOHA, and other products within the HAProxy Technologies portfolio are not impacted by this (they do not use the Spring Core library at all), you can use our products to mitigate the attack.
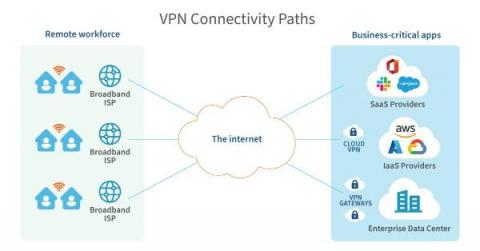
The NetOps Expert - Episode 5: Broadcom Software and AppNeta - Part 2
Up Your Network Monitoring Game with Auvik
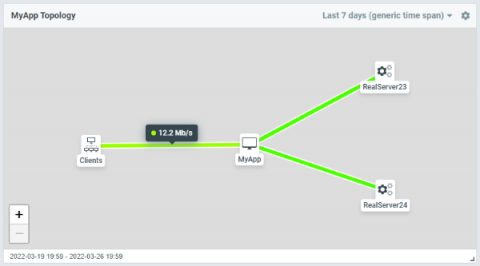
Flowmon and WhatsUp Gold: Discover application experience issues through single pane of glass
Have you ever experienced user complaints and struggled to find the root cause of the performance degradation? I'm sure every IT operations professional has. Is it the application? Is it the underlying infrastructure? Is it the network? What if you have a single pane of glass that will gather all the relevant metrics and telemetry and display it in an intuitive and easy to understand fashion?
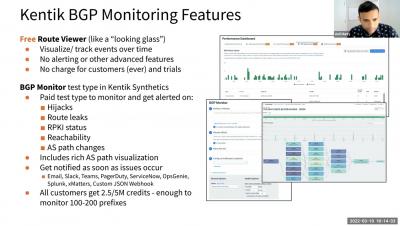
Why You Should Monitor BGP and Where to Start 031122
Sentry Points of Presence: How We Built a Distributed Ingestion Infrastructure
Event ingestion is one of the most mission-critical components at Sentry, so it’s only natural that we constantly strive to improve its scalability and efficiency. In this blog post, we want to share our journey of designing and building a distributed ingestion infrastructure—Sentry Points of Presence— that handles billions of events per day and helps thousands of organizations see what actually matters and solve critical issues quickly.
Overcoming Kubernetes Infrastructure Challenges at the Edge of the Network
In response to the explosive growth of Internet of Things (IoT) devices, organizations are embracing edge computing systems to better access and understand the enormous amount of data produced by these devices. As the name suggests, edge computing moves some storage and computing resources out of the central data center and closer to where the data is generated at the edge of the network, whether that’s a factory floor, retail store, or automated car.
Synthetics 101 - Part 2: Protecting and growing revenue with proactive monitoring
In part 1 of our synthetics series, we looked at tracking network performance to drive better business outcomes. Here in part 2 of our series, we’ll dig into the very first and most basic business outcome of using digital experience monitoring (DEM). That is, we’ll look at how to protect and grow revenue by proactively monitoring the health, availability and uptime of your critical applications and services, so you can fix issues before your customers’ experience suffers.
How Automation Simplifies Network Compliance in the Financial Sector
The global march towards delivering operational resilience across the financial sector steadily continues.