CFEngine 3.21 LTS released - Unification
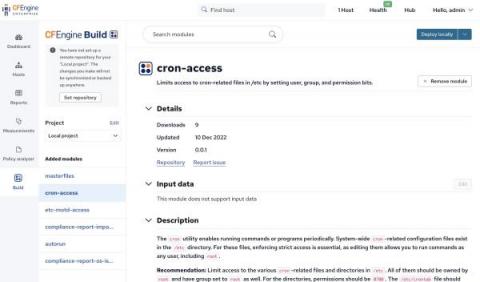
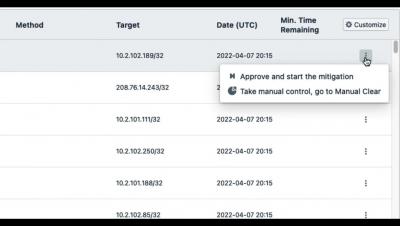
Today, we are pleased to announce the release of CFEngine 3.21.0! The focus of this new version has been unification. Across our websites and UI, you should see that it’s a much more modern and unified experience, whether you’re reading this blog post on cfengine.com, browsing the new documentation site, looking for modules on the CFEngine Build website, or adding input to modules within Build in Mission Portal.