Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on CyberSecurity for Applications, Services and Infrastructure, and related technologies.
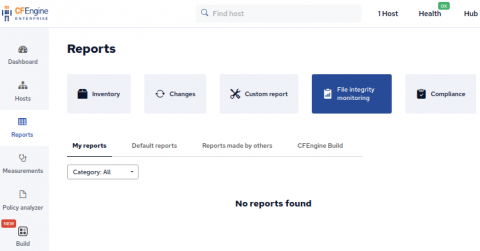
File integrity monitoring with CFEngine
File integrity monitoring is an important aspect in managing your infrastructure. Tripwire and AIDE are often cited as necessary tools by compliance frameworks1,2,3. Of course CFEngine can manage a file to make sure it contains desired content, but did you know that CFEngine also has the capability to simply monitor a file for change? In this blog post we take a look at CFEngines’ changes attribute for files promises.
Governance, Risk and Compliance for MSPs in 2023
Six Mistakes To Avoid When Mapping Your Enterprise Data Landscape
What's in store in 2023 for the tech industry?
Security holiday calendar - Part 1
As it was well received last year, we decided to do another security-focused holiday calendar this year. The concept was roughly the same, but instead of only adding security hardening modules, we’ve also added in some other security advice and blog posts to improve the variety. Now that we’re halfway through to 24 (or 25), let’s recap the first half of the calendar.
Building a Compliance Report based on inventory modules
In CFEngine Enterprise we collect information from each system in the infrastructure as inventory. Some inventory is available by default, and more can be added using modules or writing policy. You can use inventory information to create a Compliance Report with checks that determine if the information complies with your security requirements. In this blog post, we will use some modules from CFEngine Build which provide inventory data, and build a Compliance Report on top of those.
Top 5 benefits of network backup software
Grafana 9.3 feature: Grafana OAuth token improvements
As part of our efforts to improve the security of Grafana, we introduced a long-awaited feature in the latest Grafana 9.3 release that enhances Grafana’s OAuth 2.0 compatibility. The new Grafana OAuth token improvements, which are available in Grafana OSS, Grafana Cloud, and Grafana Enterprise, ensure that the user is not only logged into Grafana, but they’re also authorized by the OAuth identity provider.
The What, Why and How of Auto-Remediation in Cybersecurity
When you’re facing a cyberattack, waiting even just minutes to respond could be the difference between business as usual and a calamity. It may only take that long for threat actors to exfiltrate sensitive data or disrupt critical systems. That’s one reason why automating remediation is an essential ingredient in an effective cybersecurity strategy.