Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on CyberSecurity for Applications, Services and Infrastructure, and related technologies.
Cribl.Cloud: Are You Ready to Fly Solo?
Many years ago, I attained my private pilot’s license. This entailed completing a very structured program, similar to how most companies introduce a product to a new user. Let’s be honest, there is a really good reason for this – to avoid the crash and burn. With flight training, it’s literal, while with products it’s a bit more figurative (except when you YOLO something into production–that can cause a crash and burn–and leave for a bad first impression).
Contributing Cool Community Content to Calico
It’s right there on our community page—the statement that “Project Calico is first and foremost a community.” With that in mind, we wanted to make it easier for new contributors to get involved. It’s a win-win scenario—developers experience less frustration, they can get their work done, and have their contributions considered. Plus, the project can easily benefit from the contributions.
Macs and malware, part 2: Are Macs more secure?
Are Macs more secure? If that’s not the very definition of a clickbait headline, I don’t know what is. Spoiler warning: While I have opinions, I’m not a security expert with multiple certifications or years of experience in the field. So, I won’t take sides as to which operating system is the most secure.
Keeping IaC Secure: Common Security Risks in Infrastructure as Code
Infrastructure as Code (IaC) is the cloud-computing practice of putting the provisioning and configuring your cloud resources into machine-readable code.
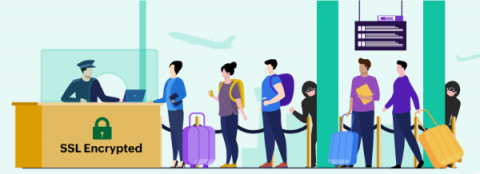
All you need to know about SSL certificate expiration
With copious amounts of data getting added across online platforms, safeguarding data and ensuring a secure environment are concerns among business entities. To offer a secure and reliable service, you need to identify loopholes, implement preventive measures to thwart attacks, and ensure customer data privacy. You need a valid Secure Sockets Layer (SSL) certificate to secure your online presence.
Data Obfuscation
Data Obfuscation is a way of making data unreadable or unusable if data breach occurs. It is like providing security to the data by encrypting it or masking it in order to make it unreadable even when the hackers can do a successful data breach. Data breaching is very common these days and every organization must protect its own data. Even if we cannot stop the data breach completely, we can save the data we have by means of data obfuscation.
Role Based Access Control for Kubernetes demo - Civo Academy
Automatically Update URL Blocklists in Zscaler Using Torq
Blocking access to certain URLs is a simple, effective strategy for protecting users and the network. But, in a world where new and increasingly sophisticated scams seem to appear almost weekly, the task of maintaining that list can become overly burdensome when performed manually. Torq offers a number of ways to automate URL blocklist management, reducing manual effort and speeding up response to new threats.
Effective IoT security requires collaboration and clarity
When firefighters arrive at burning buildings, they must contain the blaze, rescue inhabitants and keep calm under pressure. As IoT devices are increasingly deployed throughout cities, firefighters could have access to more information that could save more lives and lead to less lost property through use of real-time data about surroundings impacting people in need.