Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on CyberSecurity for Applications, Services and Infrastructure, and related technologies.
Benchmarking binary classification results in Elastic machine learning
Binary classification aims to separate elements of a given dataset into two groups on the basis of some learned classification rule. It has extensive applications from security analytics, fraud detection, malware identification, and much more. Being a supervised machine learning method, binary classification relies on the presence of labeled training data that can be used as examples from which a model can learn what separates the classes.
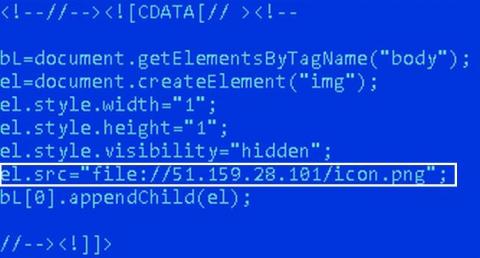
Breaking down the San Francisco airport hack
On April 7, 2020, the San Francisco International Airport (SFO) released a notice confirming that two of its websites, SFOConnect.com and SFOConstruction.com, were targets of a cyberattack in March 2020. The attack has been attributed to a hacker group that was attempting to steal the Windows logins of the airport’s employees. When we hear news about cyberattacks, a few typical, yet crucial questions spring to mind: How did the attackers perform the cyberattack?
Protecting Critical Infrastructure in Kubernetes and Rancher
“As we expand, it’s critical for our team to have both a fast and automated rollout process for each customer environment. In the end, each of our user’s access experience must be identical. Rancher is one product that’s critical to that strategy.” – Jeff Klink, VP Engineering, Cloud and Security Specialist, Sera4 Security worries keep many of us awake at night – no matter our industry.
Episode 15: Cookie Authentication in ASP.NET Core
Easily visualizing MITRE ATT&CK® round 2 evaluation results in Kibana
If you want to skip ahead to see the MITRE ATT&CK eval round 2 results visualized in an easy-to-configure Kibana dashboard, check it out here.
MITRE ATT&CK® round 2 APT emulation validates Elastic's ability to eliminate blind spots
Six months ago we celebrated the joining of forces between Endgame and Elastic under the banner of Elastic Security and announced the elimination of per endpoint pricing. Simultaneously, while the newest members of Elastic Security were getting acquainted with the Elastic SIEM team, a few of our analysts were locked away in an office at MITRE HQ for round 2 of MITRE’s APT emulation.
Ransomware: How to Combat a Growing Threat to Your Organization
Ransomware is a serious threat to institutions of all kinds, resulting in mounting costs for organizations that must literally pay ransom to regain access to their essential systems. A ransomware attack takes place when a cybercriminal denies an organization access to the data it needs to conduct business, usually by encrypting the data with a secret key. The attacker then offers to reveal the encryption key in exchange for a payment. The payment can vary in amount or kind.
Between Two Alerts: Phishing Emails - Don't Get Reeled In!
Potential attackers are really good at what they do. Security analysts see this firsthand with the amount of phishing emails their organizations see daily. A newly released State of the Phish report reveals that nearly 90% of organizations dealt with business email compromise (BEC) attacks in 2019. End users reported 9.2 million suspicious phishing emails globally for the year.
SQL Server, Part 2: Authentication and authorization mechanisms in SQL Server, simplified
In the previous blog of this series, we discussed how monitoring SQL Server activities helps secure databases. The database security can further be reinforced by carefully configuring the authentication and authorization mechanisms for database accesses. In this blog, we’ll briefly explain the various authorization and authentication mechanisms of SQL Server and some best practices you can follow.