Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on CyberSecurity for Applications, Services and Infrastructure, and related technologies.
AWS GuardDuty Monitoring with Logz.io Security Analytics and the ELK Stack
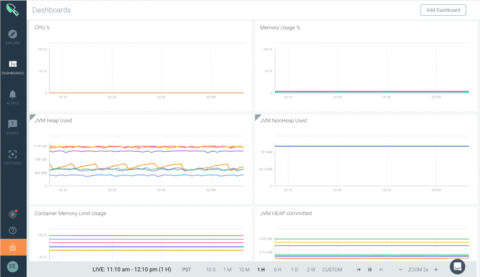
Last month, we announced Logz.io Security Analytics — a security app built on top of the ELK Stack, offering out-of-the-box security features such as threat intelligence, correlation, and premade integrations and dashboards. In this article, I’d like to show an example of using both the ELK Stack and Logz.io Security Analytics to secure an AWS environment.
Exploring Nordcloud's Promise to Deliver 100 Percent Alert-Based Security Operations to Customers
We are a multi-cloud managed services provider (MSP) that works strictly with Amazon Web Services (AWS), Google Cloud Platform (GCP) and Microsoft Azure. We’ve been working with enterprise public cloud leaders in Europe since 2012 and our goal is to provide fully managed public cloud transformation to our customers.
Five cybersecurity best practices to follow in 2019
Research by Cybersecurity Ventures predicts ransomware alone will cost businesses around the world more than $11.5 billion in 2019. What’s worse, this same study also predicts businesses will experience a cyberattack every 14 seconds by 2019, up from once every 40 seconds in 2016. So what can you do to mitigate the increasing threat of cyberattacks? Here are five IT security best practices that can help.
Falco 0.13.0 Released: Kubernetes Audit Events Support
We recently released Falco 0.13.0, which is probably the most exciting release since Falco’s 0.1.0 release almost two and a half years ago. With 0.13.0, we’re adding support for a second stream of events — Kubernetes Audit Events. This release also lays the groundwork for additional event sources to be easily added.
29 Docker security tools compared
There are quite a few Docker security tools in the ecosystem, how do they compare? We have gathered a list of the most popular Docker security tools so you can evaluate what fits your needs better, including features and use cases. Here you will find both open source projects and Docker security commercial vendors.
Improving the Signal-to-Noise Ratio in Threat Detection
Companies are generating massive amounts of data every minute. It’s impossible, unrealistic, and cost-prohibitive for analysts to spot every threat. That’s why even though breaches are in decline year over year, the first quarter of 2018 saw 686 breaches that exposed 1.4 billion records through hacking, skimming, inadvertent Internet disclosure, phishing, and malware.
Building an ELK Based SOC using Logz io Security Analytics
Advanced Mitigation Techniques to Stop DDoS Attacks in Their Tracks
In our last blog post, we learned what the Distributed Denial of Service (DDoS) attack is, and examined the DDoS picture globally. As we walked through some recent and well-known cases, we also surveyed a range of attack types and drilled down to specific examples. In this article, we’ll study the mitigation techniques you’ll need to resist these attacks. You’ll learn: 1. How to avoid becoming a bot; 2. How to prepare your own network for the possibility of an attack and finally; 3.
Monitoring and securing Kubernetes-based healthcare services on Google Cloud: Cota Healthcare
As Cota Healthcare moved to Kubernetes on Google Cloud, it chose Sysdig for Kubernetes monitoring and container security. With Sysdig, Cota accelerates healthcare service development, improves capacity planning, fixes issues rapidly, and strengthens its security posture.