Operations | Monitoring | ITSM | DevOps | Cloud
Microsoft Teams Monitoring Best Practice + Tips & Tricks
Security configurations-Part one: 7 reasons why security configurations are crucial to your security blueprint
Security configurations are security-specific settings used to secure heterogeneous endpoints such as servers, desktops, laptops, mobile devices, and tablets. As endpoints in your network diversify, securing each endpoint becomes a challenge. One way to ensure effective endpoint security is by automating it, which is where security configurations come into play. Security configurations are utilized to secure and control every facet of your network.
Avoiding Memory Leaks in NodeJS: Best Practices for Performance
Memory leaks are something every developer has to eventually face. They are common in most languages, even if the language automatically manages memory for you. Memory leaks can result in problems such as application slowdowns, crashes, high latency, and so on. In this blog post, we will look at what memory leaks are and how you can avoid them in your NodeJS application. Though this is more focused on NodeJS, it should generally apply to JavaScript and TypeScript as well.
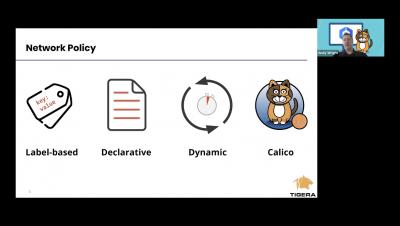
How to Deploy an Azure Kubernetes Cluster with AKS
At the end of October 2017, Microsoft announced the release of Azure Kubernetes Service (AKS), its hosted version of Kubernetes. If you’re new to AKS and curious about how to get a proof of concept (PoC) set up in your environment, read on. In this AKS tutorial, you’re going to learn, step-by-step, how to get an Azure Kubernetes cluster built with AKS.