Operations | Monitoring | ITSM | DevOps | Cloud
The State of Event-Driven Automation
Talking about competition can be hard. It’s understandable. Product positioning can be touchy subjects especially when those use cases overlap. In the DevOps space, event-driven architectures are certainly not a new concept. Companies like Netflix, LinkedIn, and Facebook have in-house tools built specifically for this type of automation. However, Relay’s mission is make it easy for everyone to build event-driven workflows – not the Netflix-es of the world.
Mattermost | The Last Five Years | June 2020
Understand Complex Environments Without Being an Expert Using AppOptics for APM
I Can Do That, Dave: Exploring AIOps
4 ways to use Catchpoint to drive remote workforce productivity
IT professionals are now adapting to a remote environment and learning to manage a distributed, homebound workforce. From a technical standpoint, the process of setting up a remote workforce is well-known. For this blog post let’s dive into one step of the process, which is arguably the most important, user experience monitoring.
Introduction to security monitoring
Security Information Monitoring or Security Event Monitoring is part of Security Information Management. Yes, I acknowledge they are flashy names and that even experts have their differences about concept and scope. Here in Pandora FMS, flexibility is part of our name, so, hereby, I will abbreviate it as Security Monitoring. As you can see, it is short and manageable!
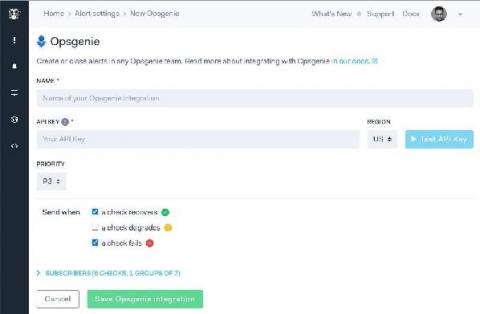
Changelog: Opsgenie, Dashboard improvements, Terraform and more
Here is an overview of the features & fixes we released over the last ~2 months.
Enabling DevSecOps with the Elastic Stack
Software development and delivery is an ever-changing landscape. Writing software was once an art form all its own, where you could write and deploy machine code with singleness of purpose and no concern for things like connecting to other computers. But as the world and the variety of systems that software supports became more complex, so did the ecosystem supporting software development.
Machine learning in cybersecurity: Detecting DGA activity in network data
In Part 1 of this blog series, we took a look at how we could use Elastic Stack machine learning to train a supervised classification model to detect malicious domains. In this second part, we will see how we can use the model we trained to enrich network data with classifications at ingest time. This will be useful for anyone who wants to detect potential DGA activity in their packetbeat data.