Operations | Monitoring | ITSM | DevOps | Cloud
Ensuring compliance with DISA STIGs, NIST 800-53, CMMC, and RMF
This blog is the second in a four-part series on infrastructure automation for government agencies that are modernizing digital systems while grappling with budget and staffing constraints and the challenges of COVID-19.
Using Audit Logs For Security and Compliance
Developers, network specialists, system administrators, and even IT helpdesk use audit log in their jobs. It’s an integral part of maintaining security and compliance. It can even be used as a diagnostic tool for error resolution. With cybersecurity threats looming more than ever before, audit logs gained even more importance in monitoring. Before we get to how you can use audit logs for security and compliance, let’s take a moment to really understand what they are and what they can do.
GDPR Compliance With Uptime.com | What You Need to Know
Uptime.com is GDPR compliant as of 2021. Becoming GDPR compliant required an organization-wide dedication to maintaining privacy and security to meet these new standards. These updates impact everything from working with support to our team logging in for work each day. Today, we’ll tackle what GDPR means to our organization, how these changes affect your usage of Uptime.com, and what we’re doing now (and into the future) to protect your personal data.
Datadog on Security and Compliance
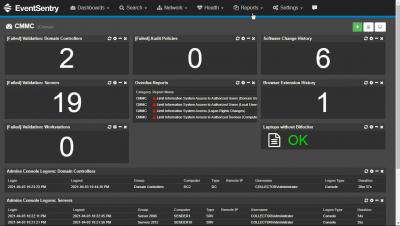
CMMC compliance with EventSentry
Automating STIG compliance and reporting
Applying the Roles and Profiles Method to Compliance Code
How to set up Software Security and Compliance for Your Artifacts
Applying the Roles and Profiles Method to Compliance Code
Most of you are familiar with the roles and profiles method of writing and classifying Puppet code. However, the roles and profiles method doesn’t have to exist only in your control repository. In fact, as I’ve been developing Puppet code centered around compliance, I’ve found that adapting the roles and profiles method into a design pattern to Puppet modules makes the code more auditable, reusable, and maintainable!