Operations | Monitoring | ITSM | DevOps | Cloud
Latest Blogs
Reputation Matters - Nexthink's Execs Share Favorite Customer Stories
Perhaps one of Nexthink’s most endearing qualities is that it has never been a “drink the kool-aid” type of company. Yes, we are proud to be the leading experience management platform in IT, but that honor is most championed from outside, not within. From its beginnings, Nexthink has been used by enterprise IT to narrow the gap between what employees expect at work and what they receive.
Logging for DevSecOps
Logging is probably not the first item to come to mind when most of us think about DevSecOps, a term that refers to the integration of security into DevOps processes, but it should be. Logging and log management play a critical role in helping to put DevSecOps principles into practice by ensuring that developers, IT operations staff, and security teams have the visibility and communication pipelines they need to prioritize security at all stages of the DevOps delivery cycle.
What is Logstash?
In this article, we are going to have a quick introduction to Logstash, a very popular application for collecting, processing and filtering log data – and see how it works. We will review plugins, installation and configuration of Logstash, we will briefly mention Beats, and also compare Logstash to other log collectors and review Logstash alternatives.
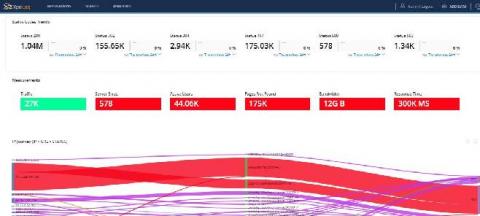
Event Chaos or Enrichment? BigPanda's CTOs Can Help You Decide
In our recent “IT Ops Demystified – Event Chaos or Enrichment?” webinar our field CTOs discuss how enrichment can help reduce operational costs by an order of magnitude. Here is a quick overview of all the goodness that you’ll be watching.
What is SRE?
Site Reliability Engineering (SRE) is a practice for managing the reliability of systems that began at Google in the early 2000s. Ben Treynor Sloss from Google started the first SRE team and coined the name.
Our 6 Favorite Automated Testing Tips
Test automation helps increase development speed while reducing cost and effort. In this article, we will share how to automate testing to help keep a test automation initiative on the right track with key tips for test execution, design and maintenance for large enterprise applications.
Robotics Recap: Learning, Programming & Snapping ROS 2
Robotics@Canonical puts a strong focus on the migration from ROS to ROS 2. ROS 2 benefits from many improvements, especially robot security. Our goal is to make it easy for you to transition to ROS 2, whether you’re completely new to ROS or a seasoned engineer retooling for a new environment. Your new platform should be secure-by-default, and we expect you’ll need to pivot between different environments as you migrate from ROS to ROS 2.
How Artificial Intelligence is Shaping the Industry of VPN
Artificial intelligence refers to the machine's ability to learn and think. Given that it sort of mimics how humans think and reason, AI's application is virtually endless. AI reduces human error, do a task that is risky for humans to do, help humans solve complex, and so much more. With the emergence of artificial intelligence, concerns about data privacy have been brought into the light. Artificial intelligence relies on our personal information to learn.
What is a Status Page? (& How Does It Benefit Companies/Customers)
There’s nothing worse than turning on your computer to start the work day and discovering the internet is down. We all know the frustration of tediously trying to figure out what’s wrong before finally breaking down and calling our service provider and waiting on hold, only to discover that it’s a known issue and it’s being addressed. What if there was a better way?