ZSB Series Mobile App Overview | Zebra
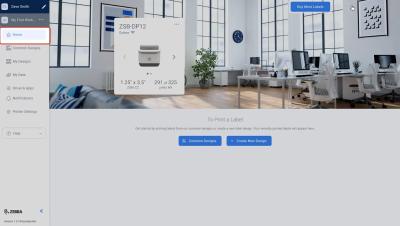
Watch this video to learn how easy it is to navigate around the ZSB Series mobile app. Learn how to log in, understand your Home screen, access and customize your label designs, add printers, manage notifications, and adjust printer settings. You’ll also discover how to personalize your workspace and ensure a seamless experience across different devices.