Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on DevOps, CI/CD, Automation and related technologies.
Applying Lessons Learned from Baking Pizza to Kubernetes Observability
Baking a delicious pizza in a wood-fired oven requires a combination of skill, experience and the right tools. The same is true for achieving optimal observability in a Kubernetes environment. In this post, we'll explore some of the lessons learned from baking pizza in a wood-fired oven and apply them to the world of Kubernetes observability.
Modernizing LinkedIn's Traffic Stack | Sanjay Singh & Sri Ram Bathina
Hosted StatsD vs. StatsD
When you are designing and building applications, you should consider how to monitor them once they become live. You do not want to be blindsided by errors and degrading performances as you operate them. When your applications fail to provide optimal performance, it can broadly impact your business. Engineers will often be distracted to investigate and fix the issues. Customers will complain. It can eventually hit your bottom line.
What are Azure Native Services?
Azure native services are cloud-based solutions that are developed, managed, and supported by Microsoft. These services are designed to help organizations build and deploy applications on the Azure cloud platform, and take advantage of the scalability, security, and reliability of the Azure infrastructure. In this blog post, we’ll take a look at some of the key Azure native services that are available, and how they can be used to build and run cloud-based applications.
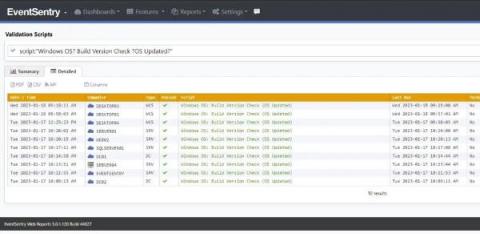
The Life of the Sysadmin: A Patch Tuesday Story
The System Administrator! AKA the Sysadmin. The keeper of the network, computers – well basically all things technology. The one who is hated for imposing complex passwords and other restrictions, but taken for granted when everything works well. They are the first to be called when “facebuuk.com” reports: “domain does not exist”.
Ubuntu 18.04 LTS End Of Life - keep your fleet of devices up and running
Ubuntu 18.04 ‘Bionic Beaver’ is reaching End of Standard Support this April, also known sometimes as End Of Life (EOL). This distribution of Ubuntu was installed by millions of users and powers up thousands of devices. From kiosks and appliances to IoT devices and robots, 18.04 helped many companies deploy innovations to the world. As with all other Ubuntu LTS releases that reach their end of standard support, Bionic Beaver will transition to Extended Security Maintenance (ESM).
A DWDM Guide: Definition, Benefits, and When You Should Use It
Today’s telecom, cable, and data providers constantly compete to provide the best, most reliable service to customers, while investing in the right technologies to maintain the integrity of data and enable the separation of users. Because of this, service providers often spend countless hours searching for cost-effective, yet future-proof solutions that fit their business needs. This is where DWDM comes in.
Introducing Project and Workspace Access Tokens
Supercharging ITSM Collaboration with Mattermost and ServiceNow
Mattermost’s core mission is to provide secure collaboration for technical teams. To do so, we concentrate on providing a collaboration layer that powers key technical and operational workflows for our customers. A prime example of this focus is the new ServiceNow integration for Mattermost, which weaves together key ServiceNow ITSM features such as Incident, Change and Problem management with Mattermost’s rich collaboration features.