Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on DevOps, CI/CD, Automation and related technologies.
The Catchpoint Open Source Software (OSS) Program
Catchpoint has always embraced new technologies and ideas. We offer a powerful monitoring platform with advanced features such as tracking digital performance from across the globe, capturing analytical data and the ability to get notified across various channels. With all these inbuilt features in hand, Catchpoint encourages its customers to build new monitors and integration that consumes monitoring data that are tailored to specific use cases.
Restore authority with Token Bandwidth Controls!
Now you can go beyond measuring your bandwidth usage and regain control via Cloudsmith's new bandwidth controls for Entitlement tokens. You can craft tokens with individual usage limits using the UI, API, and CLI, allowing you to decide the exact level of usage for each token. Combining the new and existing limits for entitlement tokens, allowances are configurable to provide fine-grained control for any combination of properties.
Best Practices: Onboarding Jfrog Xray
Gain Better Visibility into Kubernetes Cost Allocation
Adopting Kubernetes and service-based architecture can bring many benefits to organizations – teams move faster and applications scale more easily. However, visibility into cloud costs is made more complicated with this transition. This is because applications and their resource needs are often dynamic, and teams share core resources without transparent prices attached to workloads.
Introducing Puppet Enterprise tasks and workflows in Puppet Remediate
Today we are pleased to announce the release of Puppet Remediate 1.4. This release brings together the dynamic vulnerability data and prioritization capabilities in Puppet Remediate with Puppet Enterprise’s industry-leading automation to help organizations improve their security posture and reduce the risk of security incidents.
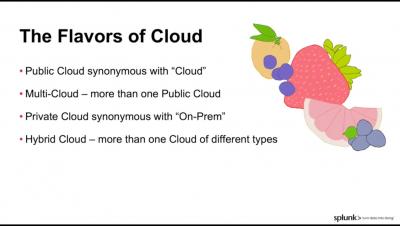
The Cloud
How to monitor istiod
Istio is a service mesh that enables teams to manage traffic in distributed workloads without modifying the workloads themselves, making it easier to implement load balancing, canarying, circuit breakers, and other design choices. Versions of Istio prior to 1.5 adopted a microservices architecture and deployed each Istio component as an independently scalable Kubernetes pod. Version 1.5 signalled a change in course, moving all of its components into a single binary, istiod.
New Microsoft partnership embeds Datadog natively in the Azure portal
We are excited to announce a new partnership with Microsoft Azure, which has enabled us to build streamlined experiences for purchasing, configuring, and managing Datadog directly inside the Azure portal. This first-of-its-kind integration of a third-party service into a public cloud provider reduces the learning curve for using Datadog to monitor the health and performance of your applications in Azure—and sets you up for a successful cloud migration or modernization.