Operations | Monitoring | ITSM | DevOps | Cloud
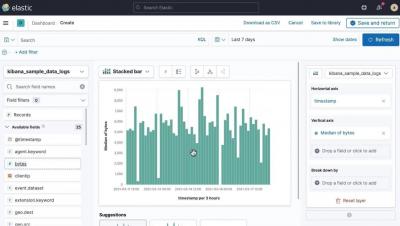
Building your first visualization with Kibana Lens
Kibana is your window into the Elastic Stack. It allows you to visualize the data that sits in Elasticsearch. In this video, you will learn how to use Kibana Lens to build your first dashboards and visualizations.
How to build a customized Artifactory image?
How to build a customized Artifactory image? This video goes over how to use a docker file to create your own customized Artifactory image, in case the base image is missing tools/content. By Matthew Wang - JFrog support
10x development speed with local serverless debugging
Serverless is great but a lot of it is in the cloud and in all these different services. Oftentimes we hear serverless developers struggle with debugging serverless locally in order to iterate fast. Without an effective debugging setup, they are left frustrated with slowed development cycle time and decreased operational efficiency. In this 45-minute hands-on webinar, we'll be discussing how to debug serverless locally to really speed up your development cycle.
Automated Kubernetes Optimization with Helm
See how Helm can be used to automatically configure the optimal resource specification for each Kubernetes (K8s) container, whenever an application is installed or upgraded.
Cloud 66 Feature Highlight: Archived Application
Archived Applications allows developers to "park" an application at any time. Archiving an application saves the configuration and state of your deployment, turns your servers off, and puts your application into a dormant state. Once your application is archived, you will not be able to open, edit or access it until you restore it. Servers used by this application will be turned off (deactivated) but not deleted. Please do not delete these servers, or you will not be able to restore your application. Note that you don't pay Cloud 66 for applications that are archived.
Kubei walk-through: A Kubernetes Runtime Vulnerabilities Scanner - Milind Chawre
Kubei is a vulnerabilities scanning and CIS Docker benchmark tool that allows users to get an accurate and immediate risk assessment of their kubernetes clusters.
Bits of Security, Snyk.io: Stranger Danger: Finding Security Vulnerabilities Before They Find You!
Open source modules on the NPM ecosystem are undoubtedly awesome. However, they also represent an undeniable and massive risk, since you’re introducing someone else’s code into your system, often with little or no scrutiny. The wrong package can introduce critical vulnerabilities into your application, exposing your application and your user's data. This talk will use a sample application, Goof, which uses various vulnerable dependencies, which we will exploit as an attacker would. For each issue, we'll explain why it happened, show its impact, and—most importantly—learn how to avoid or fix it.
Bits of Security, PedidosYa: Fraud Detection using Datadog and Sherlock
From day one, most organizations,especially the big ones, are targeted with a broad range of attacks. These range from information exfiltration attempts to fraud. Although a great majority of them can be addressed with the help of a Web Application Firewall, there are some that require more extensive tooling. Join me as I show you how we use Sherlock and Datadog to block 30,000+ fraudulent users per week in seconds. We will also discuss other applications and how you can implement similar solutions.