Sponsored Post
5 Security Logging and Monitoring Mistakes to Avoid
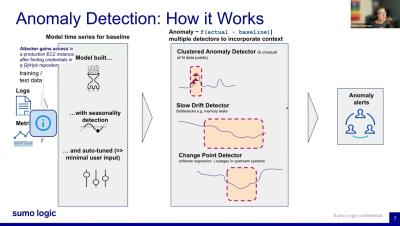
As cybersecurity attack vectors evolve, security logging and monitoring are becoming even more important. Effective logging and monitoring enables organizations to detect and investigate security incidents quickly. Cloud-based attackers are getting more sophisticated, and often rely on stolen credentials to escalate privileges and move laterally within corporate IT networks. Many do so undetected, which is why modern IT systems require a watchful eye on log data to detect suspicious activity and inform incident response efforts.