Monitor and diagnose network performance issues with SNMP Traps
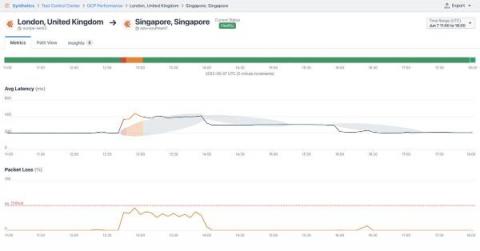
Monitoring your on-premise or hybrid infrastructure means keeping track of potentially thousands of devices, any one of which could be a point of failure. Additionally, silos between application and network teams can create visibility gaps that complicate troubleshooting. For network engineers investigating bottlenecks, being able to view real-time infrastructure health and performance data alongside application metrics is essential for ensuring their organizations meet key SLOs.