Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on CyberSecurity for Applications, Services and Infrastructure, and related technologies.
Three countries, outside the European Community, that are reforming their privacy policies
Are you not a little curious? Even a little bit, right under your chin or your temple about how they deal with privacy policies in other countries? Aren’t you? Well, surprise! Today, in Pandora FMS blog, we are going to get it out of our system by discussing how they do it, how they deal with the protection of international data and privacy, in at least three countries outside the European Community.
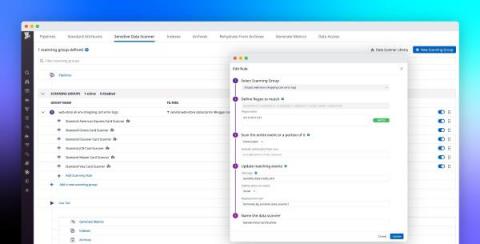
Build a modern data compliance strategy with Datadog's Sensitive Data Scanner
Within distributed applications, data moves across many loosely connected endpoints, microservices, and teams, making it difficult to know when services are storing—or inadvertently leaking—sensitive data. This is especially true for governance, risk management, and compliance (GRC) or other security teams working for enterprises in highly regulated industries, such as healthcare, banking, insurance, and financial services.
Fast and simple troubleshooting with GUI-based Dynamic Packet Capture
With the Calico 3.10 release, Dynamic Packet Capture is available in Dynamic Service Graph. This means users who require self-service, live troubleshooting for microservices and Kubernetes workloads can capture and evaluate traffic packets on endpoints without writing a single line of code or using any 3rd-party troubleshooting tools. Users don’t need to learn about or have knowledge of kubectl or YAML to troubleshoot their microservices and Kubernetes cluster.
Label standard and best practices for Kubernetes security
In this blog post, I will be talking about label standard and best practices for Kubernetes security. This is a common area where I see organizations struggle to define the set of labels required to meet their security requirements. My advice is to always start with a hierarchical security design that is capable of achieving your enterprise security and compliance requirements, then define your label standard in alignment with your design.
How Secure Tenancy Keeps Your Secrets Secret
The best way to be sure that you keep a secret is not to know it in the first place. Managing secrets is a notoriously difficult engineering problem. Across our industry, secrets are stored in a bewildering variety of secure (and sometimes notoriously insecure) systems of varying complexity. Engineers are often trying to balance the least worst set of tradeoffs. At Honeycomb, we asked: What if we didn’t need to know your secrets to begin with?
What is CMMC? + Useful Resources, Communities & Expert Advice
In this guide, we are covering the facts that you need to know in order to prepare your business to tick off the necessary boxes required to meet CMMC compliance.
How to Automate the Handling of Suspicious User Behavior
We live in a technological society, and cyber attacks are on the rise. Much of this fraudulent activity is linked to malicious actors or gangs of cyber criminals who are trying to exploit anything they can get their hands on. By using tools like Cobalt Strike or customized alternatives, they attempt to penetrate an organization's defenses in order to gain leverage, exfiltrate PIIs, plant ransomware or CnC beacons, or perform other kinds of malicious acts.
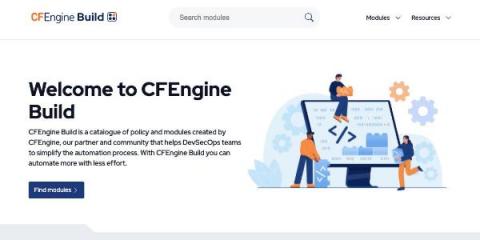
Announcing CFEngine Build
Earlier this year, we hinted at what we were working on - a place for users to find and share reusable modules for CFEngine. Today, the CFEngine team is pleased to announce the launch of CFEngine Build: The new website, build.cfengine.com, allows you to browse for modules, and gives you information about how to use each one of them. When you’ve found the module you were looking for, it can be downloaded and built using the command line tooling.
Bupa protects and connects 4.7M customers with digital healthcare
The future of healthcare is personalized, joined services shaped by actionable insights. That relies on building secure digital health services that customers can trust. Cyberattacks are getting more sophisticated and harder to detect, and the damage to businesses and their reputations can be difficult to recover from. Although security is complex, resources can be scarce. Getting the best return on investment is crucial to balance protecting customer data with safeguarding service delivery.