Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on CyberSecurity for Applications, Services and Infrastructure, and related technologies.
The 7 Stages of the Client-Side Hacking Lifecycle
The threat of your customers being attacked directly on the client-side is more real today than ever before. Magecart are knocking on everybody’s door – you, your 3rd parties, and even their 4th parties. This is happening continuously, with Magecart looking for opportunities to steal your valuable data for sale on the dark web. It’s a complex and ever-changing problem. So what stage are you at in the customer hacking lifecycle?
Halloween Cyber Street - Zero day attacks
RapidSpike Magecart Detection
Sysdig Secure Overview
Running Cloud-Native Workloads In Production with Sysdig
Canonical and IBM on Technology Enablers for Financial Services
Pod Security Policies in production with Sysdig's Kubernetes Policy Advisor
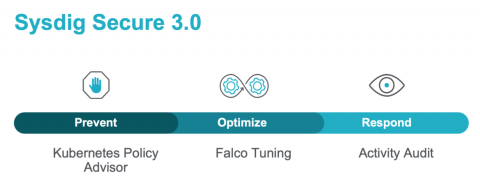
Sysdig Secure 3.0 introduces Kubernetes Policy Advisor to provide Kubernetes native prevention using Pod Security Policies (PSPs). This feature automates the generation of PSPs and validates them pre-deployment, so they don’t break applications when applied. This allows users to adopt Pod Security Policies in production environments quickly and easily.
Sysdig Secure 3.0 introduces native prevention and incident response for Kubernetes
Today, we are excited to announce the launch of Sysdig Secure 3.0! Sysdig Secure is the industry’s first security tool to bring both prevention and incident response to Kubernetes.
CloudSploit Joins the Aqua Family
We are pleased to announce that CloudSploit has joined the Aqua Security family. Aqua is the leading platform provider for securing container-based, serverless, and cloud native applications. CloudSploit rounds out its offering by adding our open-core Cloud Security Posture Management (CSPM) SaaS.