Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on CyberSecurity for Applications, Services and Infrastructure, and related technologies.
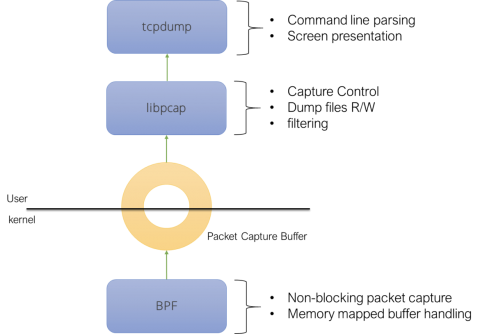
Understanding common library implementation
As Falco grows in popularity, many new users get exposed to it on a daily basis. As should be expected, most of these users are not aware of what the architecture underneath Falco is. What components play a role in powering it? How do these components relate to each other? I thought it would be fun to write a blog post that answers these questions. And I thought it would be fun to write it with an historical perspective.
ManageEngine recognized for Next Gen Unified Endpoint Management in London
“With cybercrime heading into the tens of billions of records stolen, and trillions of dollars in damages, we are proud to recognize ManageEngine as an award-winning innovator that offers a new approach to defeat these criminals,” said Pierlugi Paganini, editor-in-chief, Cyber Defense Magazine.
Load Up and Drive Cloud DevSecOps on Azure
At JFrog, we think enabling DevSecOps in the cloud should be as easy as ordering from a drive-up window. Getting the tools you need for digital transformation should only be a short stop on your long journey. And you should be able to get it your way, on the cloud services platforms you choose. That’s why we’re excited to announce the availability of JFrog Cloud Pro X on Azure Marketplace.
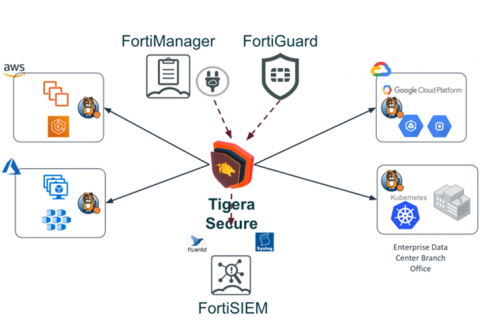
Tigera Joins the Fortinet Fabric-Ready Program and Partners with Fortinet to Secure Kubernetes Environments
We are proud to partner with Fortinet and join their Fabric-Ready Technology Alliance Partner program. With this partnership, Fortinet customers will be able to extend their network security architecture to their Kubernetes environments. Our partnership was driven from interest from Fortinet’s customers to protect their Kubernetes based infrastructure. Kubernetes adoption is growing like wildfire and nearly every enterprise on the planet is at some stage of their Kubernetes journey.
Magecart Monthly: Halloween Special
October brings Halloween and National Cybersecurity Awareness Month, however, it has also been one of the scariest months for Magecart attack discoveries! Here’s the latest news on Magecart and other website attacks, with insights from our own Security Researcher!
Data Privacy Is Our Birthright - national cybersecurity month
Never before in history has the concept of identity been so vital. To a large extent, everything we rely on to live our lives depends on who we are… or perhaps more accurately, who we can prove ourselves to be. Our data has come to be the standard by which we define ourselves. Because this identity-defining data is online, the protection of our data is of paramount importance.
Multi-cluster security with Falco and AWS Firelens on EKS & ECS
In this blog post, we are going to teach you how to aggregate all Kubernetes security events across your AWS container services. We’ll be using AWS FireLens to route Falco notifications, centralizing all the security events, such as AWS CloudWatch, in one service.