Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on CyberSecurity for Applications, Services and Infrastructure, and related technologies.
Compliance Made Easy with JFrog Xray
As compliance managers, we often find ourselves in a struggle. Our responsibility is to uphold compliance standards but in order to achieve this, we need to “sell” the concept to the relevant stakeholders, inter alia the business teams and R&D. We’re put in the position of justifying required changes and processes and are thus mistakenly perceived as business “stoppers” and not enablers.
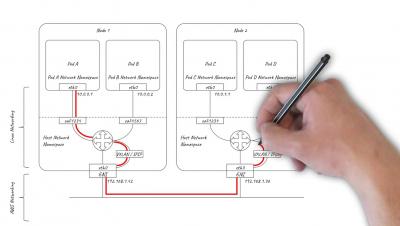
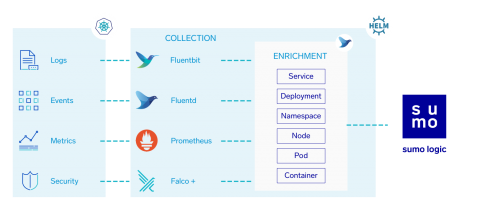
Kubernetes DevSecOps with Sumo Logic
With Sumo Logic, we can put all of these pieces together to build end-to-end Observability in Kubernetes.
Threat Intelligence And Log Management: Security Through Automation
The constant evolution of security threats has long-since made preventing cyber-attacks and network intrusion attempts a nearly impossible task. Real threats are often hard to identify among a multitude of false alarms, and many experts understand that a well-integrated and fully-automated threat intelligence strategy is the best approach. Nevertheless, 70% of security industry professionals still believe threat intelligence to be too complex and bulky to provide actionable insights.
Android malware: How do enterprises tackle this ever-growing menace?
Let us first agree on a couple of things before we start: One, Android is the most affordable platform for enterprises with a mobile-first/mobile-only workforce, and it has the smallest learning curve of any mobile OS. Two, due to its very open-source nature, Android is easy for malicious actors to pray on, with the Google Play Store being the breeding ground for many attacks.
SolarWinds Launches Identity Monitor to Empower IT and Security Pros with Automated Account Takeover Prevention
Continuum Navigate East 2019: 4 Cybersecurity Takeaways
5 Tips for Preventing Ransomware Attacks
You don't need to be a cybersecurity expert to know that ransomware attacks have become one of today's greatest IT security threats. From WannaCry to the attack against the city of Atlanta, major ransomware exploits have become so commonplace in the last few years that they may seem impossible to avoid. Fortunately, preventing ransomware is far from impossible. Let's take a look at a few strategies you can put in place to mitigate your risk of becoming part of the next ransomware statistic.
Tracking Malicious Activity across the Sumo Attack Lifecycle
Magecart Monthly: New Targets - Hospitality, Transport and Retail Industries
Here’s the latest news on Magecart and other website attacks! We’ve trawled the web for the latest news of data breaches, including updates on previous attacks with insights from our own Security Researcher.