Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on CyberSecurity for Applications, Services and Infrastructure, and related technologies.
Now or never: Your last stand against cyber attacks.
Account Takeover IS Your Problem
Sentry Receives SOC 2 Compliance Certification
In a world where companies’ security teams are notoriously—and rightly—paranoid, we’re pleased to announce that Sentry has recently received its SOC 2 Type I compliance certification. Having met this important industry standard on the effectiveness of a company’s internal controls around information security, our existing and future customers can be confident about their data security and integrity with Sentry.
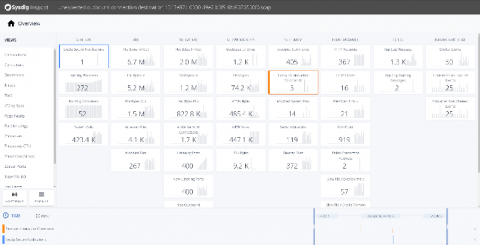
Sysdig Announces the Cloud-Native Security Hub is Available
Announcing the Cloud Native Security Hub
One of the main benefits to standardized infrastructure is the ability to share application resources across entities. We are taking advantage of this with the Cloud Native Security Hub as we start to explore how to standardize cloud native security.
Security Policy as Code Now Fully Automated with Calico Enterprise 2.6
We are excited to announce the general availability of Calico Enterprise 2.6 (formerly known as Tigera Secure). With this release, it is now possible to fully-automate Security-Policy-as-Code within a CI-CD pipeline, including the ability to implement security as a Canary rollout, which is the most critical requirement to automating network security.
Bar Hofesh - AppSec in the DevSecOps world
Visa Security Alert for New Self-Cleaning Skimmer - Pipka
Visa have reported a new security alert for an advanced, self-cleaning, JavaScript skimmer named Pipka. The security researchers at Visa’s Payment Fraud Disruptions (PFD) discovered the skimmer in September earlier this year. The skimmer was first seen on a North American ecommerce website which had previously been infected with a different skimmer, Inter. Visa have now identified another 16 additional sites with hosting the Pipka code.
Securing Google Cloud Run serverless workloads
Google Cloud Run is a serverless compute platform that automatically scales your stateless containers. In this post we are going to showcase how to secure the entire lifecycle of your Cloud Run services. Sysdig provides a secure DevOps workflow for Cloud Run Platforms that embeds security, maximizes availability and validates compliance across the serverless lifecycle. Sysdig Secure Devops Platform is open by design, with the scale, performance and usability enterprises demand.