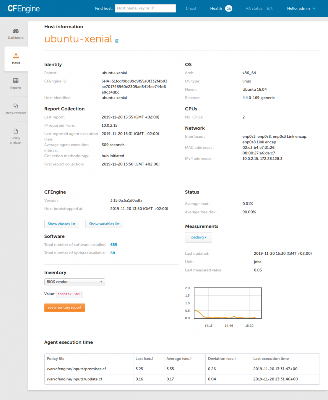
CFEngine 3.10.7 LTS and 3.12.3 LTS released
We are now happy to release two new LTS versions of CFEngine, 3.10.7 LTS, and 3.12.3 LTS. This will be the last release of the CFEngine 3.10 LTS series. Standard Support of CFEngine 3.10 LTS ends end of this year. If you would like extended support, please contact us. From the CFEngine release schedule, we see that CFEngine 3.10 LTS is maintained and supported until December 28th, 2019.