Operations | Monitoring | ITSM | DevOps | Cloud
Tip of the Day - Keeping Employees Productive
HAProxy
The Power of Open Source Software: Rancher Academy Issues 1,000th Certificate
The Rancher Academy launched on May 15, 2020. Here we are, 94 days later, and we’ve issued our 1,000th certificate to a graduate of the Certified Rancher Operator: Level 1 course. Rancher is open source software, so anyone can download it and use it. With that freedom, though, comes a cost: we all learn how to use it according to how we need to use it. Through this lens, the actual potential of Rancher becomes distorted, and the experience of each individual varies widely.
How to Secure the network of your GKE Cluster
How to be a successful project owner (without micromanaging)
Connecting the dots for security analysts
Purchase Management-Driven Transformation: Efficient ITAM Begins Here
Growth is generally considered to be a healthy characteristic of a business. But, if the firm cannot establish systems that can take care of that growth, it might end up digging a hole for its operations.
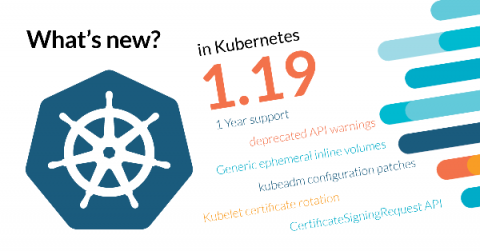
What's new in Kubernetes 1.19?
Kubernetes as a project is maturing, support has been increased from nine to 12 months, and there’s a new protocol in place to ensure a steady progress on feature development. Also, many of its new features are meant to improve the quality of life of its users, like Generic ephemeral inline volumes, or the structured logging.