Operations | Monitoring | ITSM | DevOps | Cloud
JFrog Artifactory on Your Choice of Cloud Provider
How to Provision Cloud Infrastructure
One of the best things about cloud computing is how it converts technical efficiencies into cost-savings. Some of those efficiencies are just part of the tool kit, like pay-per-use Lambda jobs. Good DevOps brings a lot of savings to the cloud, as well. It can smooth out high-friction state management challenges. Sprucing up how you provision cloud services, for example, speeds up deployments. That’s where treating infrastructure the same as workflows from the rest of your codebase comes in.
How to tag deployments with Sleuth
Automatically (or manually) tag your Sleuth deployments
All deployments are not created equal, but you'd never know it from your Slack channel notifications. In reality, some deployments you really care about, as they contain things like API changes or database migrations, and you want that information to surface. We created tags in Sleuth for this very reason. Out of the box, Sleuth matches files in your deployment with known patterns, and if any are found, tags your deployments automatically.
Who's calling - A neighbor or a fraudster?
Once upon a time the telephone system was a trusted method of connecting people. While we now spend more time on our phones than ever, our relationship to phone calls has changed -- we’re hesitant to answer calls from unknown phone numbers, often because we think the call is a con. But what if the caller ID is spoofed/modified and made to look like a telephone number that you may trust or a number with a local area code and familiar prefix?
Enforcing Enterprise Security Controls in Kubernetes using Calico Enterprise
Hybrid cloud infrastructures run critical business resources and are subject to some of the strictest network security controls. Irrespective of the industry and resource types, these controls broadly fall into three categories. Workloads (pods) running on Kubernetes are ephemeral in nature, and IP-based controls are no longer effective. The challenge is to enforce the organizational security controls on the workloads and Kubernetes nodes themselves.
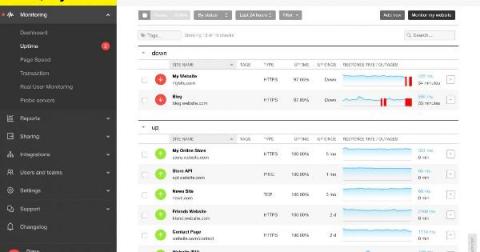
How to Spot Website Errors and Reduce Troubleshooting Time
Adapting Your Cybersecurity Habits With Ivanti Neurons
Tuesday morning you roll out of bed, turn off your alarm, tiptoe down the stairs, retrieve your paper, flip the hallway lights on, feed the dog, and start making coffee—in five minutes. Performing this series of early-morning tasks is called chunking. Certain neurons in the brain “bookend” the habit for you, signaling the routine has started (the alarm) and ended (coffee).
community.icinga.com
The community forum is a place where you can meet and chat with other Icinga users. It’s hosted by Icinga and moderated by both the Icinga team and members of the community. It’s mostly being used as a platform to ask and answer technical questions about Icinga, which is a great way to learn more about the tool stack! What does it look like? It’s a discourse platform, so it’s a collection of threads or topics which are open for anyone to leave a comment on!