Operations | Monitoring | ITSM | DevOps | Cloud
Detailed view on Azure Function Custom Handlers
Manage logs from multiple clouds and on-premises workloads together
We’ve heard from our customers that you need visibility into metrics and logs from Google Cloud, other clouds, and on-prem in one place. Google Cloud has partnered with Blue Medora to bring you a single solution to save time and money in managing your logs in a single place. Google Cloud’s operations management suite gives you the same scalable core platform that powers all internal and Google Cloud observability.
GitKraken vs Sourcetree
Software developers, students, and a few sea creatures have spoken. GitKraken is the most popular Git GUI in the world—named the most used graphical user interface for Git in the 2020 State of the Software Development Report. You might, however, be on the fence; maybe you’re Git-curious, but not sure whether to ‘commit’ (sorry) to a GUI. After all, there are several out there. Which one should you choose?
Puppet Camp Germany: Configuring Highly Scalable Compile Masters
The Application Performance Monitoring Journey
One of the best parts of our job is enabling you to become the best #ITPerformanceHero that you can be. But behind the scenes, eG Innovations is filled with talented team members who wear their own IT Hero capes. We want to take some time to introduce you to some of the people who make eG Innovations the leading performance monitoring company on the market. We’re pleased to introduce Arun Aravamudhan, Head, APM and Web UX products.
Feature Spotlight: Auto-Tracing
Lumigo’s Auto-Tracing allows you to implement distributed tracing on your Lambda functions with 3-clicks and no manual code changes. If you’ve already decided to move to a serverless infrastructure, you probably understand the importance of monitoring your AWS Lambdas and what it might entail. For the few out there that are still wondering what monitoring AWS Lambda means, I’ll break it down for you in a couple of steps.
Getting started with adding a new security data source in your Elastic SIEM: Part 1
What I love about our free and open Elastic SIEM is how easy it is to add new data sources. I’ve learned how to do this firsthand, and thought it’d be helpful to share my experience getting started. Last October, I joined Elastic Security when Elastic and Endgame combined forces. Working with our awesome security community, I’ve had the opportunity to add new data sources for our users to complement our growing catalog of integrations.
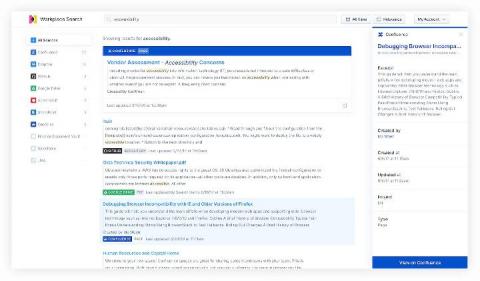
Searching Confluence with Elastic Workplace Search
For many companies, Elastic included, wikis developed with Confluence are a critical source of content, procedures, policies, and plenty of other important info, spanning teams across the entire organization. But sometimes finding a particular nugget of information can be tricky, especially when you’re not exactly sure where that information was located. Was it in the wiki? In a Word doc? In Salesforce? A GitHub issue? Somewhere else?
Maze Ransomware Attack Hits Cognizant
New Jersey-based service provider Cognizant is the latest victim of the Maze ransomware attack. This is an unfortunate reality check, proving that hackers don’t stop their calculated, malicious activities for COVID-19. Accordingly, managed service providers (MSPs) are still largely vulnerable to these malicious crimes.