Operations | Monitoring | ITSM | DevOps | Cloud
Grafana v7.0 sneak peek: auto grid layout
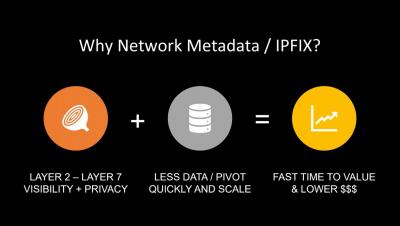
Threat Hunting with Network Metadata
Scaling OpenShift Container Resources using Ansible
Assume you have a process to determine the optimal settings for CPU and memory for each container running in your environment. Since we know resource demand is continuously changing, let’s also assume these settings are being produced periodically by this process. How can you configure Ansible to implement these settings each time you run the associated playbook for the container in question?
The High Cost of NOT Monitoring Every Business-Critical Application
Remote Monitoring to Support Employees Working from Home
The recent COVID-19 outbreak is stressing healthcare systems worldwide. Most countries are looking to “flatten the curve” of new cases in order to allow the sick to be treated without swamping hospitals.
How PagerDuty and Partner Rundeck Enable Business Continuity for Digital Operations
At times like these when the world has been forced to adapt and go almost entirely digital, it’s imperative that our systems and platforms stay up and operational—all the times. We are going to great lengths to make sure that the hardware and software in our application stacks are reliable and responsive. Hardware is set up to have redundant backups and new code is tested and reviewed to make sure it doesn’t introduce any bugs into the system.
How to choose servers for your company
You’ve been thinking all morning. You keep wondering how to choose servers for your company. All right, think the answer will be almost always: What do you need them for? And the choice of servers will depend on the functions that they will fulfill, and these are also likely to be related to the size of your company.
Benchmarking binary classification results in Elastic machine learning
Binary classification aims to separate elements of a given dataset into two groups on the basis of some learned classification rule. It has extensive applications from security analytics, fraud detection, malware identification, and much more. Being a supervised machine learning method, binary classification relies on the presence of labeled training data that can be used as examples from which a model can learn what separates the classes.
Darwin Was Right: Change Will Separate the Strong from the Weak
“It is not the strongest or the most intelligent who will survive, but those who can best manage change” said Charles Darwin over 150 years ago – and probably every IT Ops engineer out there these days would agree with him. According to Gartner (and probably your experience as well), over 80% of service disruptions these days are caused by changes in infrastructure and software.