Protect your organization against Adrozek
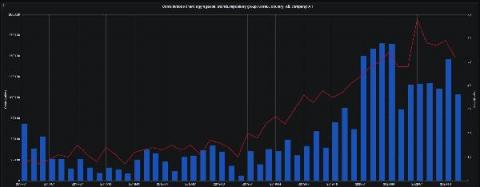
Adrozek is a malicious browser modifier that, when installed on users’ machines, infects them with adware. This particular strain of malware has been making rounds since May 2020; according to Microsoft, it was at its peak in August, when as many as 30,000 computers were affected per day. Although classified as adware, Adrozek is also designed to collect information extracted from browsers by modifying browser settings and extensions.