Operations | Monitoring | ITSM | DevOps | Cloud
JFrog Pipelines 1.6: Overcoming CI/CD Obstacles to Scaling DevOps
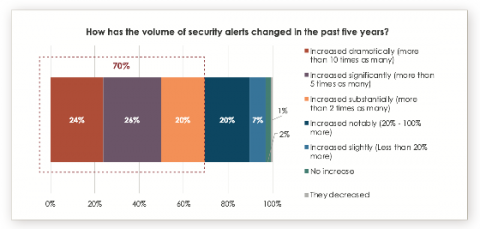
SRE Report 2020 - Balancing 'Dev' and 'Ops'
We recently released Catchpoint’s SRE Report 2020 that analyzed results from the SRE survey we conducted early this year along with a recent addendum survey. The report offers a detailed look at the current state of SRE and how the shift to an all-remote work environment has impacted SRE teams. In this blog, we take a deeper look at one of the report highlights – ‘Heavy Ops Workload Comes at a Cost’.
Postmortems and More With J. Paul Reed
PagerDuty sat down with J. Paul Reed, a Senior Applied Resilience Engineer at Netflix, for an Ask Me Anything (AMA) to discuss best practices around postmortems. Reed is a prominent speaker and advocate of DevOps and operations complexity, and has over 15 years of experience in release engineering. His background in tech, along with his previous work at companies like Mozilla and VMware, give him a unique perspective into the inner workings of innovative organizations.
Pandora FMS 747 Release
These release notes describe new features, improvements and fixed issues in Pandora FMS NG 747. They also provide information about upgrades and describe some workarounds for known issues.
macOS vs. Windows - What kernels tell you about security events: Part 2
This post continues this two-part blog series on further understanding the differences between macOS and Windows on the system level for effective endpoint security analysis. In Part 1, we covered process events. Here in Part 2, we’ll discuss file and network events. As with Part 1, my hope is to help cybersecurity professionals expand and enrich their experiences on a less familiar platform, ultimately helping them to be better prepared to face differences from past experiences.
Elastic Workplace Search on Elastic Cloud: Enabling greater flexibility and speed
We recently announced that Elastic Enterprise Search — our combined solution of search products — is now available to deploy as a single solution on Elastic Cloud. While Elastic App Search has been available on Elastic Cloud since early 2020, this is a new and exciting deployment option for Elastic Workplace Search.
5 Serverless AWS Core Services Everyone Should Have in Their Starter Toolkit
When first looking into serverless migration and its architecture, it can feel like you’re staring down an endless shopping aisle of critical serverless tools that all need to be put into your basket straight away. Some services seem to offer the same function, while others can feel wildly different - both, as a result, can instill some doubts as to what is really necessary for your business and serverless application.