Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on IT Networks and related technologies.
Kemp Flowmon ADS and Check Point Integration: Automated incident detection and response
We have recently published a script for the integration of the Anomaly Detection System (ADS) with a Check Point firewall. This ensures automated threat detection and response where attackers are blocked from accessing the network resources and causing even further harm. The previous integration with Fortinet describes a way of stopping the attacker at the perimeter. The following use case is largely the same, except with a Check Point firewall instead.
Maximizing voice connectivity: Microsoft Teams and Zoom Phone BYOC
3 tips to enhance remote access security
As managed services provider (MSP) technicians know, remote access gives an authorized user the ability to enter another user’s computer or network through a network connection. This access is often established via a remote desktop protocol (RDP), which is a network communications protocol from Microsoft® that is specifically designed for remote management.
Less is more: Incident management and monitoring in hybrid IT infrastructures
Many companies are continuously modernizing their infrastructure – but there is no standard way for the perfect IT infrastructure. Still, hybrid architectures have become the status quo in enterprises. Almost all organizations have migrated at least parts of their assets to the cloud or run applications as cloud services. At the same time, businesses want to dovetail their IT architecture with software development and are therefore embracing dynamic infrastructures.
Building a Network Architecture to Support the Next Phase of Remote Work
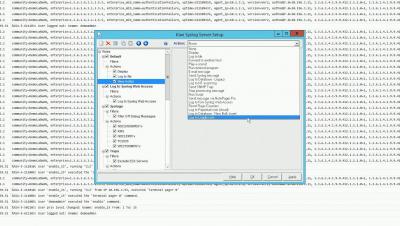
DX NetOps Network Monitoring Software Helps Reduce Noise and Increase Efficiency with New Event Filters
DX NetOps 21.2 network monitoring software continues to innovate and improve the scale, speed, and simplicity of network operations with a focused set of high-value features and capabilities. The latest release of Broadcom’s DX NetOps 21.2 network monitoring software delivers expanded capabilities to monitor and assure your software-defined networking (SDN), and network functions virtualization (NFV) deployments.
Boosting performance with network monitoring solutions
Technological advances and emerging networking concepts are constantly shaping our IT infrastructure. Networks are no longer limited to traditional networking constraints such as its static nature, but are continually evolving to improve efficiency by spanning across wired, wireless, virtual, and hybrid IT environments. This IT evolution drives organizations to advance digitally and support computational requirements to meet their business objectives.