Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on IT Networks and related technologies.
Winning On Tomorrow's Interconnected Battlefields
5 key benefits of using an IP scanner
In todays IP-centric world, it’s becoming increasingly complex to support network-intensive adaptations like cloud adoption and bring your own device (BYOD) polices. As an IT admin, you’re responsible for scanning and tracking your IP resources to ensure that network devices and end users can be allocated unique IP addresses to access your network.
Layer 4 and Layer 7 Proxy Mode
HAProxy can run in two different modes: TCP or HTTP. When operating in TCP mode, we say that it acts as a layer 4 proxy. In HTTP mode, we say that it acts as a layer 7 proxy. To understand the difference, you must first learn about the Open Systems Interconnection (OSI) model, which helps IT pros conceptualize and explain where a piece of software fits in the context of a computer network.
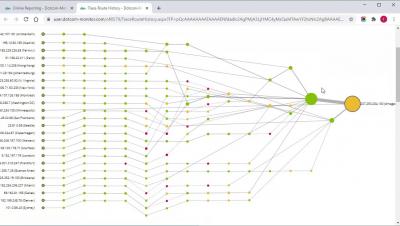
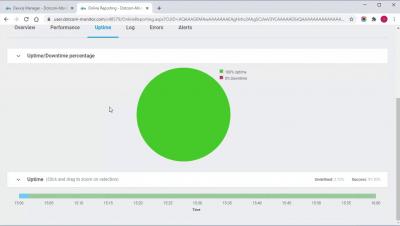
Network Assessment for A Successful IT Migration | Obkio
Load Balancing and NetSecOps - What's the Deal?
Kemp, known for its well-tuned and easy-to-use load balancer LoadMaster, has acquired Flowmon, extending its product portfolio and growing through acquisition. So you may ask, how does the technology fit?
Flowmon and Kemp Together. Why it Makes Sense
For more than a decade we have been concentrating our best talents into two areas. Improving technology and making our products available globally. Now, the time has come to massively scale up our business and technological power.