Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on CyberSecurity for Applications, Services and Infrastructure, and related technologies.
Ubuntu Confidential VMs on Azure: Introducing Ephemeral OS disks & vTPMs
The rising trend of Data Breaches and Critical Vulnerabilities in 2023
As the year comes to an end, we are taking a look back on the major data breaches and vulnerabilities that disrupted the security of both small, and large and very important organizations around the world and across all industries. According to a recently published report: As this trend is on the rise, governmental organizations and companies of every size put more emphasis on the security of their systems and networks.
How MSPs and MSSPs can reduce risk and liability for their clients
For 83% of companies, a cyber incident is just a matter of time (IBM). And when it does happen, it will cost the organization millions, coming in at a global average of $4.35 million per breach. Add to that stringent data protection laws and the growing frequency and reach of ransomware and other sophisticated attacks.
The 5 Best Vanta Alternatives for Security Compliance
Over the last two to three years, we’ve seen increasing demands on all kinds of software companies to comply with security and compliance standards. More and more organizations are looking to benefit by moving their operations to the cloud, but this increases the potential for cybersecurity attacks and breaches. A new type of compliance vendor has emerged to help companies that must comply with the security standards designed to ward off cybersecurity threats.
Detecting PowerShell Exploitation
In today’s digital landscape, cybersecurity is a top priority for organizations. Hackers are continuously finding new ways to exploit vulnerabilities and compromise systems. PowerShell, a powerful scripting language and automation framework developed by Microsoft, has unfortunately become a favored tool among attackers due to its capability to run.NET code and execute dynamic code downloaded from another system (or the internet) and execute it in memory without ever touching disk.
Securing Your Smart Home: Tips For A Safe Connected Environment
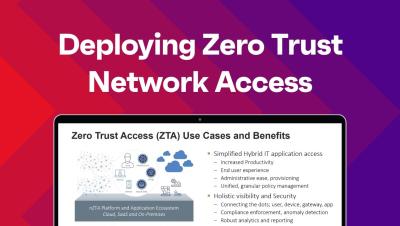
Security Webinar: A Practical Guide to Deploying Zero Trust Network Access
How to Deploy Microsoft LAPS
Securing privileged accounts is of utmost concern to cybersecurity professionals, and Active Directory, Microsoft’s identity and access management service, forms the backbone of the majority of organizations. Active Directory (AD) centralizes user accounts, computers, and resources, ensuring access control, and local administrator accounts wield substantial power within Windows systems.