Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on CyberSecurity for Applications, Services and Infrastructure, and related technologies.
Splunk SOAR Playbooks - AWS IAM Find and Disable Inactive Users
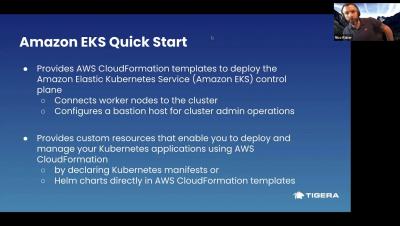
AWS Quickstart for Calico
NEW Feature: Configurable Assurance Alerts
At RapidSpike everyone gets involved with product and feature ideation, including our customers! We pride ourselves on being responsive to your needs, taking your feedback, and turning it into our next great feature — after all, you know what you need. We’re here to listen and our developers love tackling a new challenge and solving a tricky problem. This has trickled down into one of our latest features — Configurable Assurance Alerts.
The Benefits of User Journeys
Getting up and running with Calico On-Prem
Extending the Zero-Trust Security Framework to Your Home
Mixing your personal and work devices while connected to your home network and accessing the Internet is a risky proposition from a security and privacy standpoint. Why? I frequently monitor my firewall logs. What I observe on my WAN interface are blocked IP addresses sourced from adversarial nation states which makes the hair on the back of my neck stand up.
Sysdig Usage Report Finds Shifting Container Security Left is Not Enough
NEW Feature: Journey Pre-Actions
We have released a new upgrade to our script editor which is part of our ongoing commitment to build the best Synthetic User Journey monitoring tool on the market – Journey Pre-Actions. This upgrade is simple but will be useful for those websites that require certain prerequisites in order to allow tests such as these to be run. As with many of our features here at RapidSpike, this was born from a real-world requirement from a number of our customers.
Sysdig 2021 container security and usage report: Shifting left is not enough
The fourth annual Sysdig container security and usage report looks at how global Sysdig customers of all sizes and industries are using and securing container environments. By examining how and when organizations are implementing security in the development lifecycle, we have been able to uncover some interesting data points in this year’s report. For example, we can see that 74% of organizations are scanning container images in the build process.